2019-02-20 10:00:00 -0500
The latest point release update of Codebook for macOS, version 3.7.4, is mostly a well-rounded bugfix release. However, it includes some new resources for our customers who use the popular Little Snitch network monitoring and defense app.
Little Snitch monitors a Mac’s network connections, and when run in Alert mode it will prompt the user about a new network connection with a handy dialog for approving or denying it, and for creating custom and dynamic firewall rules for the future.
Normally, there’s not much Little Snitch can tell you about a particular process’s intent when attempting to access the network. There’s a lot it can tell you, but little information from the app or process itself. However, if an app is properly code-signed, and includes an Internet Access Policy file, the app can describe the various types of network requests it makes and why. That information is then made available in Little Snitch’s connection alert dialogs. An application can even include links, for instance to helpful documentation!
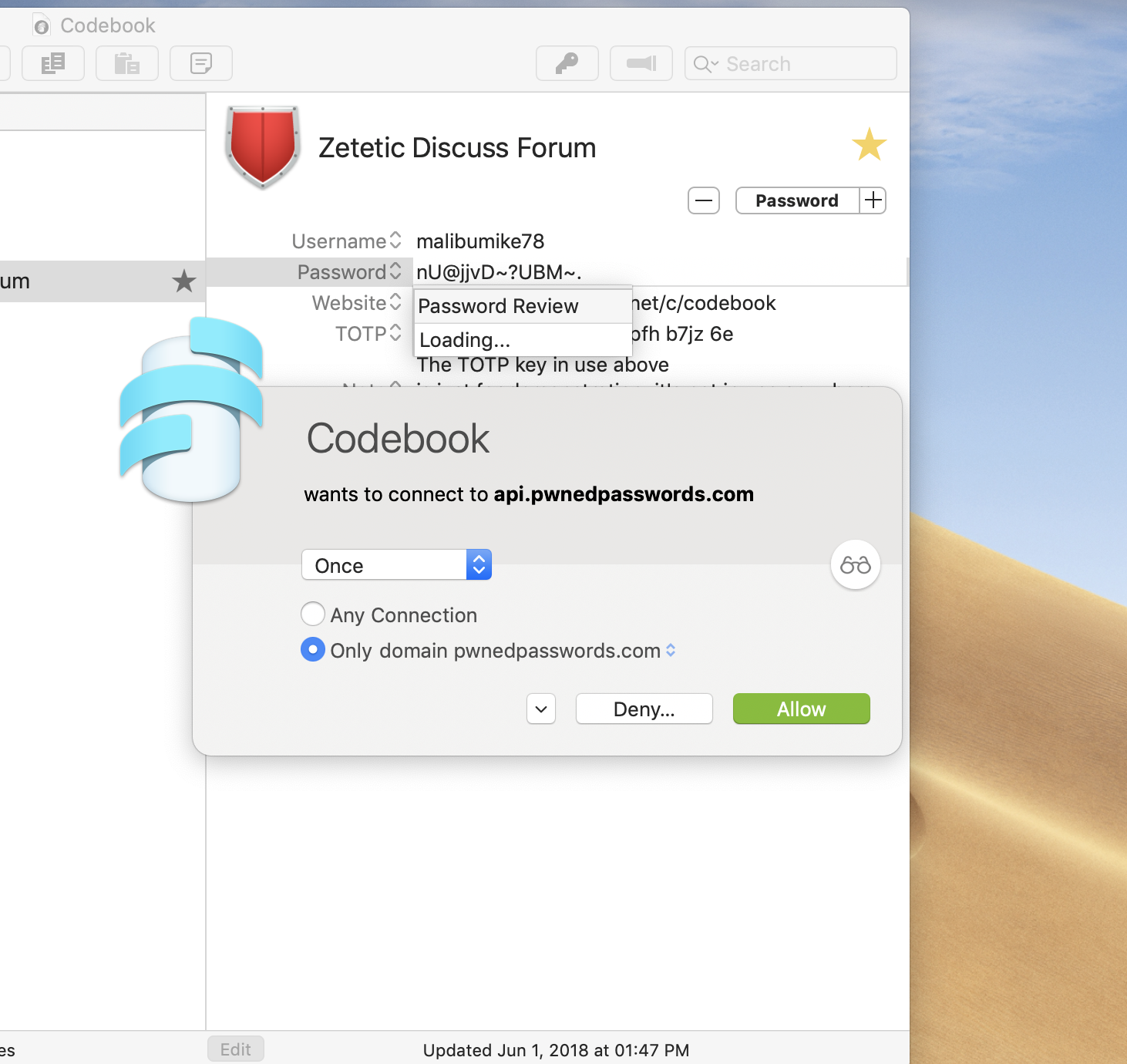
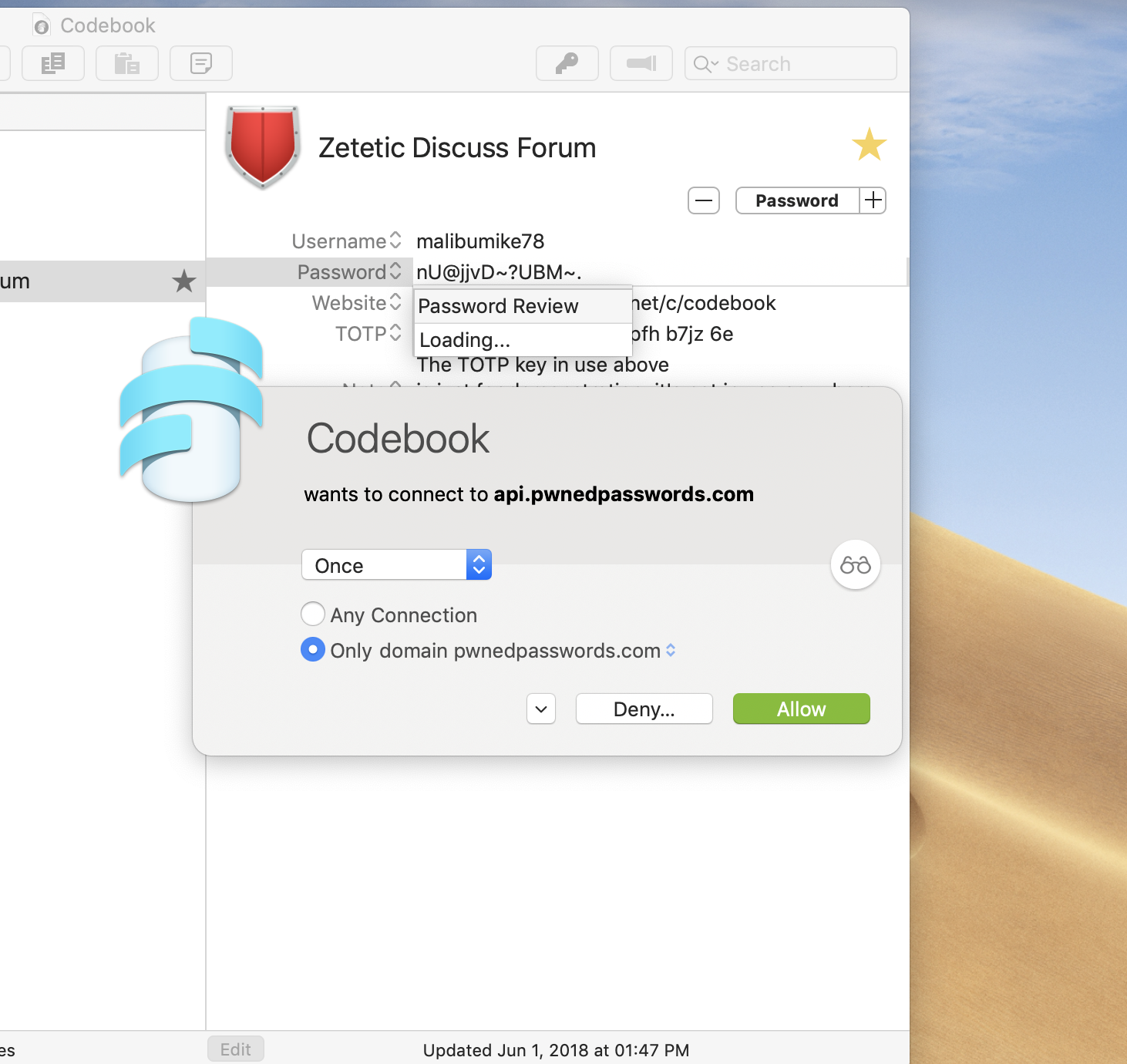
Here’s an alert from Little Snitch in response to Codebook’s Password Review feature:
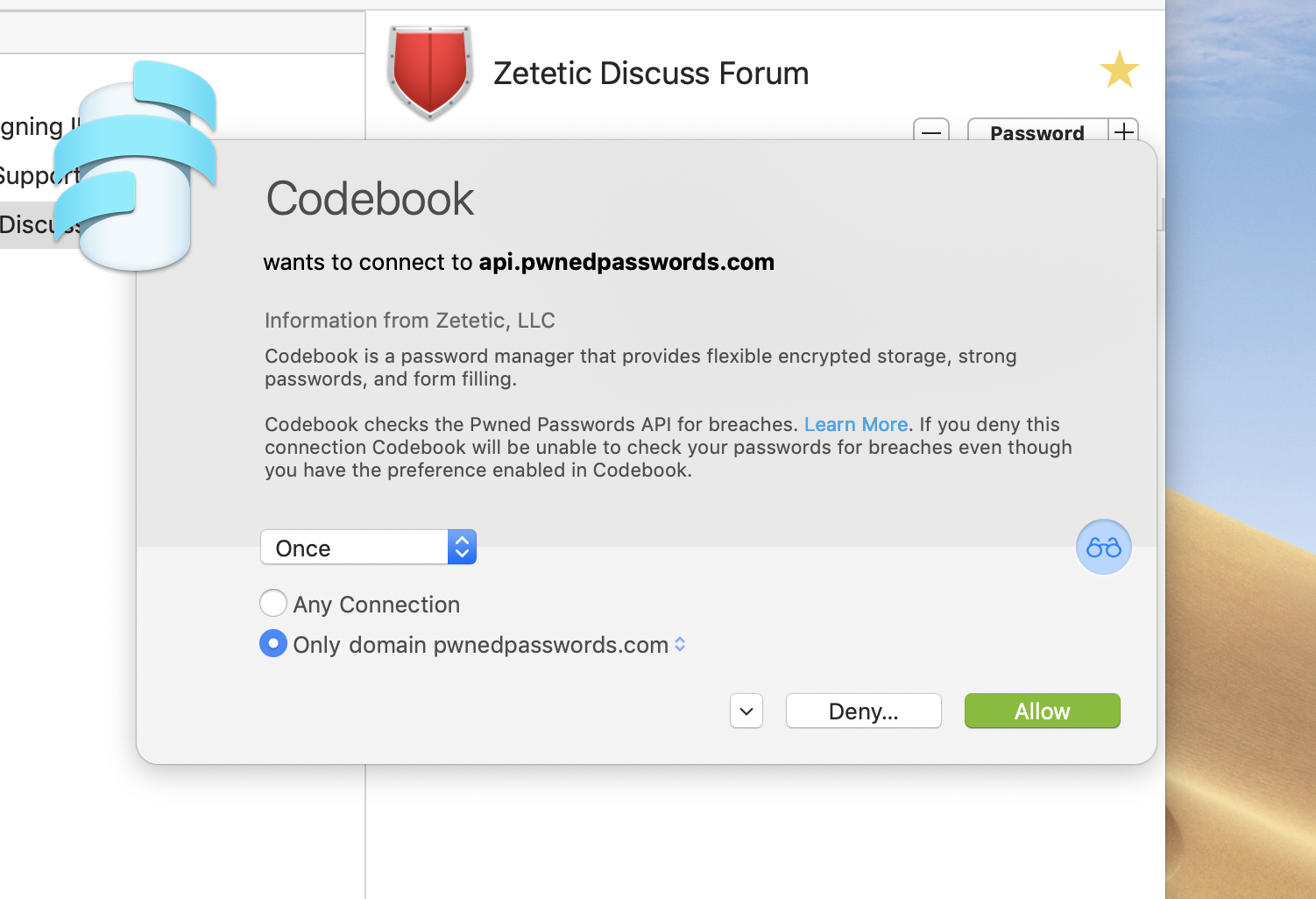
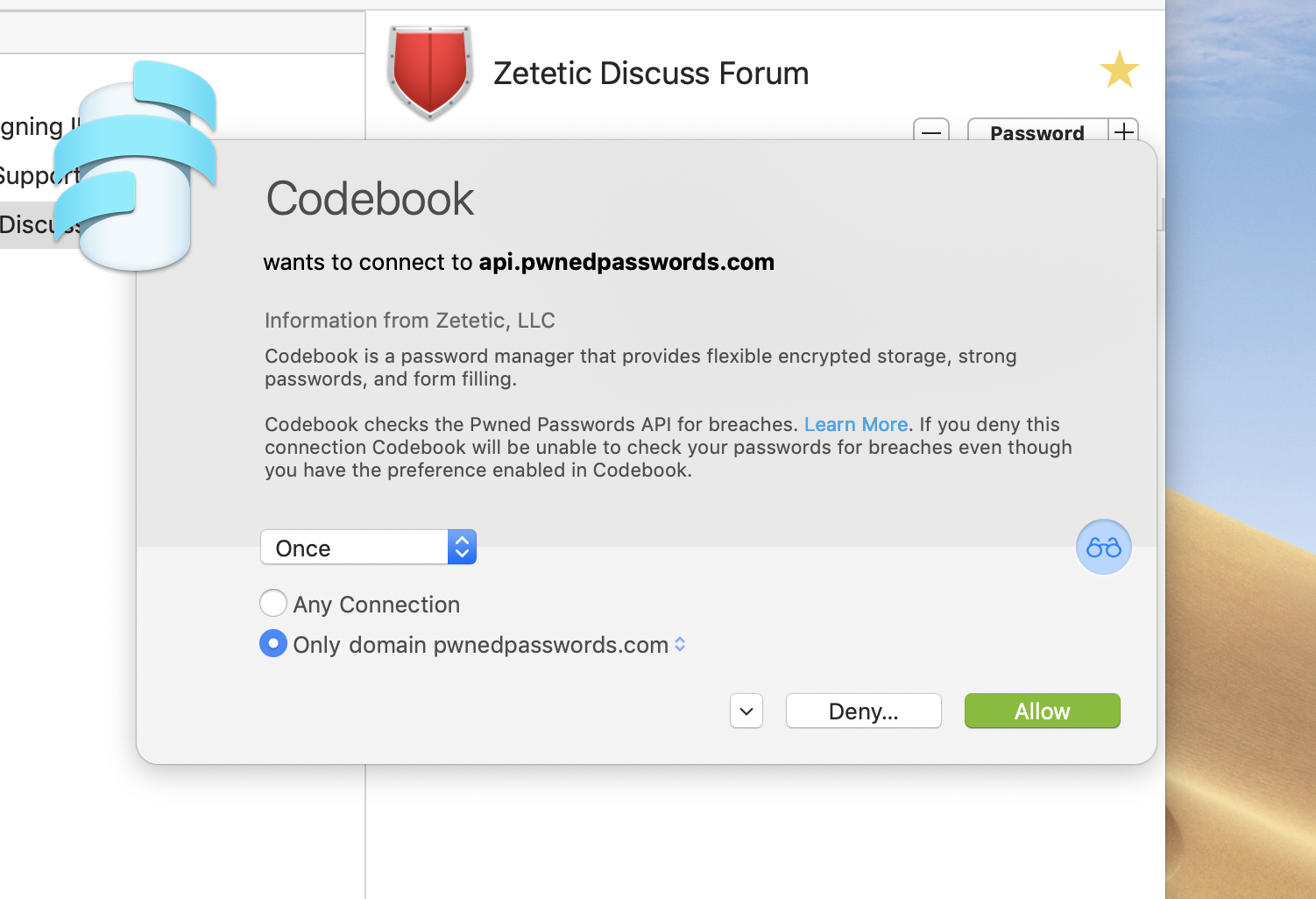
If we click on the bifocals icon to reveal the Research Assistant, we see detailed information about what’s going on, from Codebook:
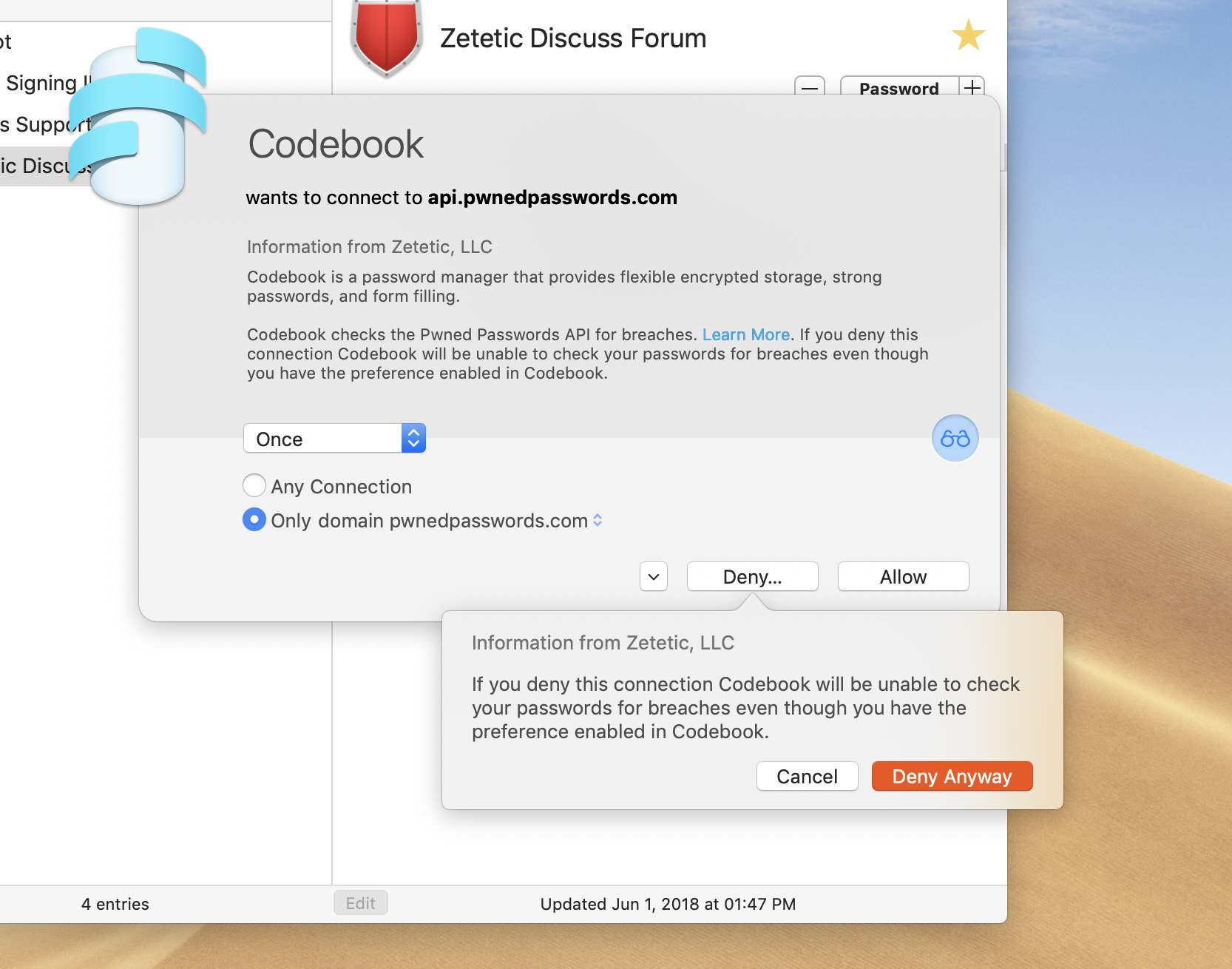
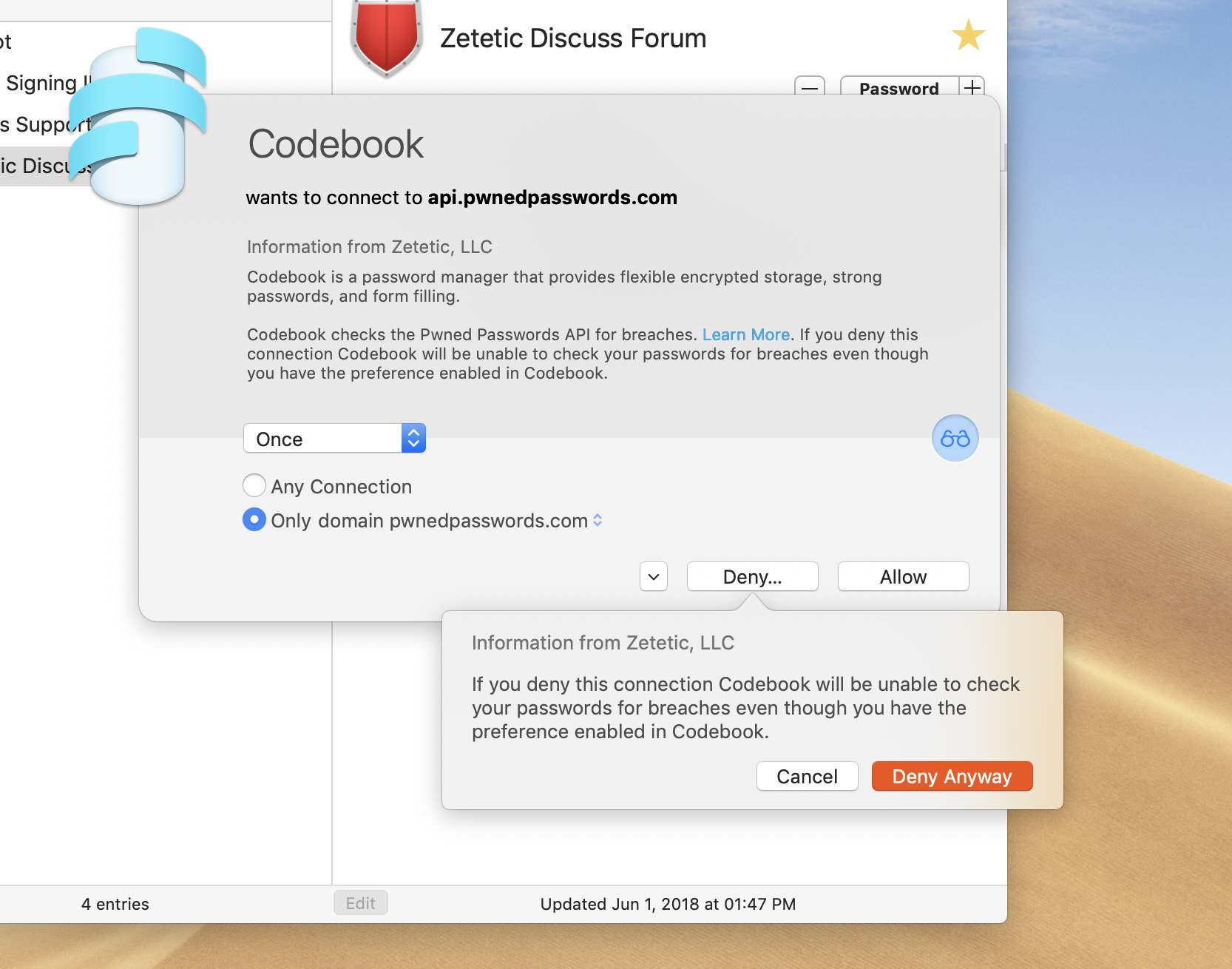
If the user clicks on the Deny button, they are presented with a quick heads-up on what will happen:
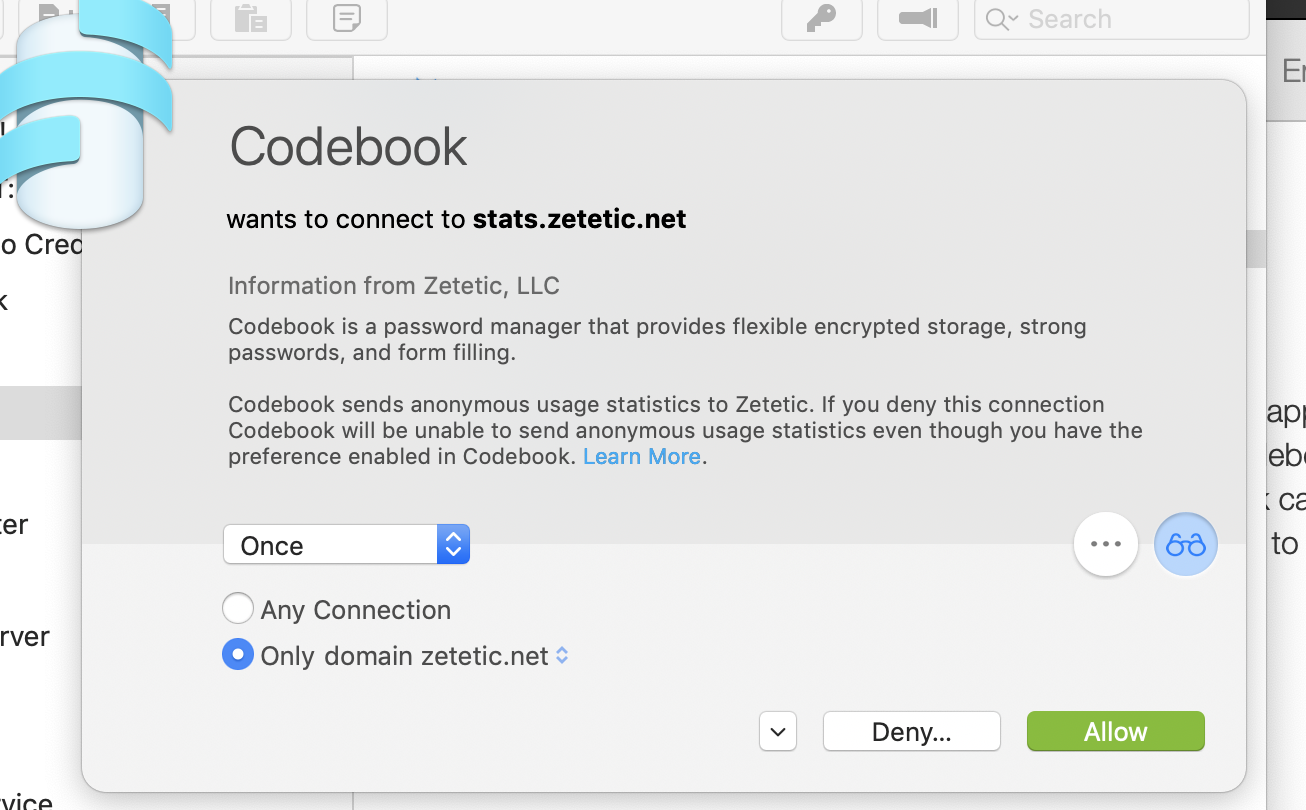
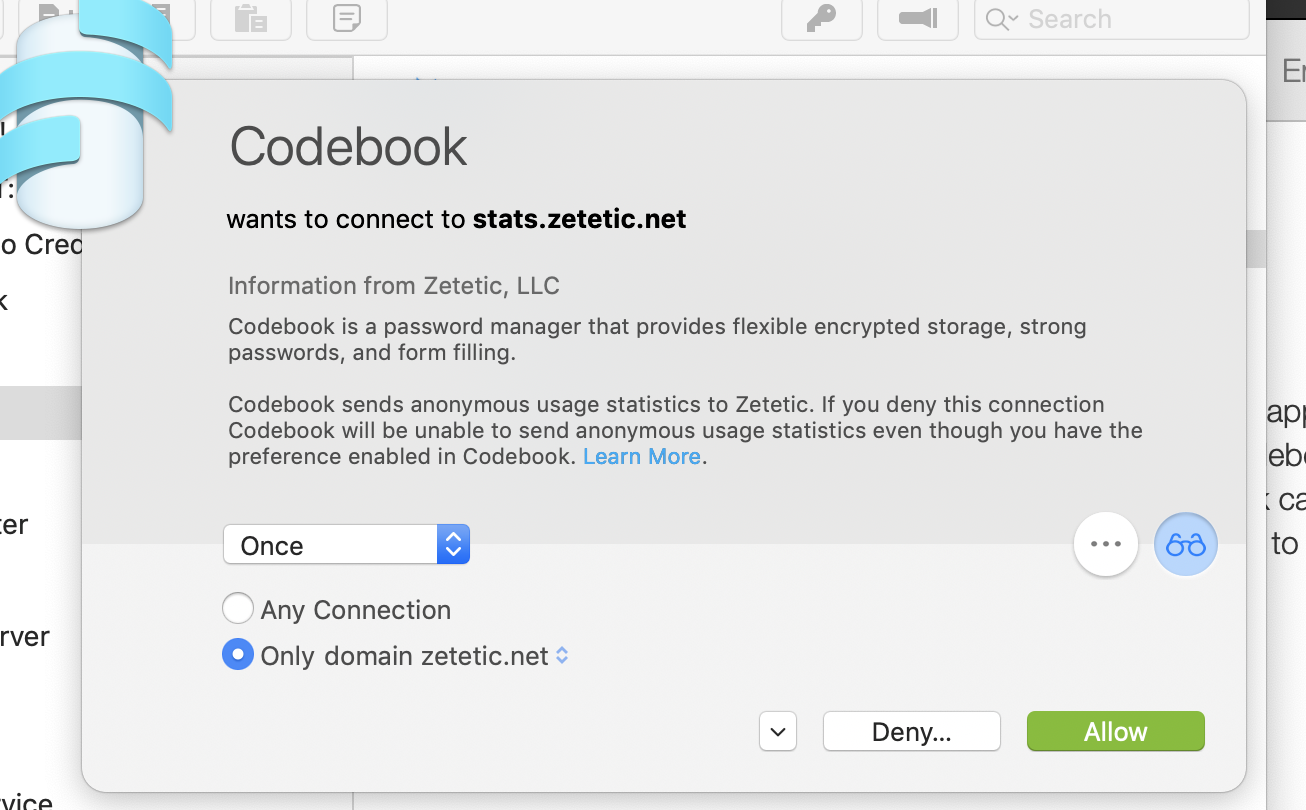
Here’s what happens when Little Snitch intercepts Codebook’s stats feature:
All in all, a simple and handy integration from Objective Development that should be quite useful to those of our customers who also use Little Snitch.
2019-01-28 12:14:00 -0500
Having arrived at the end of a process begun a little while ago now, we’ve removed Codebook Lite and Codebook for iPad from the iTunes App Store. Now there’s only one version of Codebook for iOS available, a universal app for iPhone and iPad that offers a 14-day free trial.
These companion apps served us well over the years. It was more than a decade ago—2008—that we first released our password manager Codebook (then called STRIP) for iOS (then called iPhoneOS) in the App Store. At the time it was stand-alone, only supported iPhone, and required an upfront purchase to download and run (and would stay that way for a long time).
We wanted a way to allow people to try it for free, but In-App Purchases weren’t a thing yet and trials weren’t allowed in the App Store so we did what seemed the next best thing: we created the Lite version as a separate, free-to-download app limited to ten records and no Sync feature.
The Lite approach has its limitations! Offering a clear migration path to the paid version (we did this pretty well I think), difficulty if not outright inability to track conversions from free to paid, and the limitations themselves that prevented the customer from really trying out the app realistically and on more than one platform.
Then there’s the extra work to make sure this second application target is always as up to date as the full version, with every new version of iOS, any bug fixes, and any new features. To be sure, most of the code is shared, but this additional version needed to be maintained and tested and managed in the App Store.
When the iPad arrived on the scene, developers had a choice: build a separate app targeted at the iPad only, or adapt your existing iPhone app to handle both as a universal app. At the time, it seemed like the fastest and easiest way to get Codebook going on the iPad was to go the separate app route.
So now we had a third app, with all the attendant effort required as described before regarding the Lite version! Prior to the modern automation of code signing in Xcode this created some serious challenges to getting everything built and signed properly.
A few years back we began the work of whittling this down. We adapted the main iPhone version to be a universal app supporting iPhone and iPad, and began to let customers of the iPad-only version know that it would be eventually discontinued in favor of the universal version.
Fast-forward a couple years to recent changes in how Apple allows In-App Purchases to be used, and we were finally able to offer a free trial in the main, universal version of Codebook for iOS, and last year we jumped on it.
All this is a long way of saying it feels good to say goodbye to Codebook Lite and Codebook for iPad: we’ve come a long way with Codebook for iOS! And we’re in great shape for what’s to come. All of us here at Zetetic have been working hard on Codebook 4, now the primary focus of Codebook development. It’s a big upgrade to Codebook’s security and sync features, so we’ll be doing extensive testing, and looking for more beta testers. If you’d like to become a beta tester and help us make sure we’ve got Codebook 4 just right, please email us at support@zetetic.net and let us know!
2018-12-18 07:00:00 -0500
SQLCipher 4.0.1 is now available. This update to SQLCipher 4 includes several very important changes:
- Based on upstream SQLite 3.26.0, which addresses the SQLite “Magellan” vulnerability
- Adds
PRAGMA cipher_compatibility and PRAGMA cipher_default_compatibility which simplify configuration of appropriate compatibility settings for different major SQLCipher versions
- Filters out
ATTACH statements which contain KEY parameters from readline history when using the command line shell
- Fixes a crash in the command line shell when it is provided empty input (e.g.
^D)
- Fixes various compiler warnings related to
strict-prototypes
The Magellan Vulnerability
The SQLite Magellan issue is a remote code execution vulnerability. Discovered by Tencent Blade Team, this problem can potentially affect applications that use SQLite versions prior to 3.26.0. By extension, because SQLCipher is based on SQLite, this issue can also affect applications that use SQLCipher versions prior to this release of 4.0.1.
The scope of the vulnerability is such that it could be used to exploit applications that:
- Allow a potential attacker to execute arbitrary SQL; or
- Open untrusted databases (i.e. that could be specifically corrupted by an attacker)
Due to the potential severity of this issue, we strongly recommend that all applications upgrade to SQLCipher 4.0.1, especially if they meet the aforementioned criteria.
Compatibility
As with the recent SQLCipher 4.0.0 release, 4.0.1 contains changes that are not directly compatible with SQLCipher 3.x (or lower). These provide a much higher level of security than previous versions of SQLCipher, however, SQLCipher 4.x will not open older databases by default (i.e. those created by SQLCipher 3.x or lower). To enable backwards-compatibility, applications can easily adjust settings at runtime or migrate older databases:
- To migrate and upgrade an existing database in place (preserving data and schema) to use the new default settings, use
PRAGMA cipher_migrate.
- To open an older database use the compatibility PRAGMAs to adjust settings back to their previous values. For example, to open a SQLCipher 3 database using SQLCipher 4, use the following statement after opening and keying the database:
PRAGMA cipher_compatibility = 3;.
- To attach and export data to a new database with fine-grained control, use the
sqlcipher_export() convenience function.
Please review this additional guidance for detailed upgrade and migration scenarios. We have also published a migration guide for Commercial and Enterprise customers upgrading to SQLCipher 4.x using the SQLite-net API.
Availability
Commercial Edition - On-demand access to new releases of SQLCipher Commercial Edition are available to licensees with an active CipherCare subscriber subscription, along with private, prioritized support directly from Zetetic. CipherCare subscribers will receive a separate email notification regarding the update and can contact us to request the latest SQLCipher distribution and applicable software license codes.
SQLCipher Enterprise Program - Enterprise Program Subscription customers will receive a separate email notification about the release, and the latest SQLCipher packages and license codes will be provided directly via your organization’s private online software delivery share.
Community Edition - SQLCipher 4.0.1 in source format is directly available on GitHub. The Community Edition of SQLCipher for Android is available via AAR packaging. The Community Edition of SQLCipher for iOS can be compiled from source or using CocoaPods.
2018-11-30 07:00:00 -0500
We are incredibly excited to announce the much anticipated release of SQLCipher 4. This is a major update that includes new features, improvements, and fixes. Here are some of the most important highlights:
- PBKDF2-HMAC-SHA512 is the new KDF algorithm
- HMAC-SHA512 is now used for per-page HMACs
- The default database page size has been increased to 4096 bytes
- KDF iteration count has been increased to 256,000
- Improved memory sanitization features
- Significant performance improvements for common use cases on platforms including iOS, Android, and Windows
- New baseline on upstream 3.25.2 enabling many new SQLite features
- Completely revamped client API support for .NET based platforms including sqlite-net, Entity Framework, and Microsoft ADO.NET
The full list of changes in the release can be found below. Note that changes indicated by a * are high impact and will impact compatibility with prior version of SQLCipher!
SQLCipher Core
- Default page size for databases increased to 4096 bytes (up from 1024) *
- Default PBKDF2 iterations increased to 256,000 (up from 64,000) *
- Default KDF algorithm is now PBKDF2-HMAC-SHA512 (from PBKDF2-HMAC-SHA1) *
- Default HMAC algorithm is now HMAC-SHA512 (from HMAC-SHA1) *
- PRAGMA cipher is now disabled and no longer supported (after multi-year deprecation) *
- PRAGMA rekey_cipher is now disabled and no longer supported *
- PRAGMA rekey_kdf_iter is now disabled and no longer supported *
- By default all memory allocated internally by SQLite before the memory is wiped before it is freed
- PRAGMA cipher_memory_security: allows full memory wiping to be disabled for performance when the feature is not required
- PRAGMA cipher_kdf_algorithm, cipher_default_kdf_algorithm to control KDF algorithm selection between PBKDF2-HMAC-SHA1, PBKDF2-HMAC-SHA256 and PBKDF2-HMAC-SHA512
- PRAGMA cipher_hmac_algorithm, cipher_default_hmac_algorithm to control HMAC algorithm selection between HMAC-SHA1, HMAC-SHA256 and PBKDF2-HMAC-SHA512
- Based on upstream SQLite 3.25.2
- When compiled with readline support, PRAGMA key and rekey lines will no longer be saved to history
- Adds second optional parameter to sqlcipher_export to specify source database to support bidirectional exports
- Fixes compatibility with LibreSSL 2.7.0+
- Fixes compatibility with OpenSSL 1.1.x
- Simplified and improved performance for PRAGMA cipher_migrate when migrating older database versions
- Refactoring of SQLCipher tests into separate files by test type
- PRAGMA cipher_plaintext_header_size and cipher_default_plaintext_header_size: allocates a portion of the database header which will not be encrypted to allow identification as a SQLite database
- PRAGMA cipher_salt: retrieve or set the salt value for the database
- Adds Podspec for using tagged versions of SQLCipher
- Define SQLCIPHER_PROFILE_USE_FOPEN for WinXP support
- Improved error handling for cryptographic providers
- Improved memory handling for PRAGMA commands that return values
- Improved version reporting to assist with identification of distribution
- Major rewrite and simplification of internal codec and pager extension
- Fixes compilation with –disable-amalgamation
- Removes sqlcipher.xcodeproj build support
SQLCipher for Android
- Substantial improvements to cursor access performance due to new loading heuristics
- Define custom cursor allocation sizes for paging query results, including initial, growth size, and maximum memory allocations
- Option to disable loading heuristic via setFillWindowForwardOnly on SQLiteCursor instance
- JNI CursorWindow caching of chunk pointer offsets to minimize linked list traversal
- Query total data size, and largest individual row in bytes based on provided query
- WAL mode API to enable, disable, and check if enabled
- Add API to get list of attached databases
- Add API to perform integrity check of the database
- Add API to enable, or disable foreign key constraints
- Improvements to begin transactions to allow for immediate and exclusive modes
- SQLiteOpenHelper supports onConfigure and onDowngrade callbacks
- SQLiteOpenHelper exposes the database name, and current WAL mode
- Improve exceptions thrown within JNI layer
- SQLCipher for Android target SDK set to 26
- Add support for AboutLibraries
SQLCipher for iOS
- To allow the use of WAL mode databases in shared containers use PRAGMA cipher_plaintext_header_size and cipher_default_plaintext_header_size to allocate a portion of the database header which will not be encrypted to allow identification as a SQLite database.
- Major (2x or more) performance improvements with hardware acceleration on 4K page size databases
- Removes support for sqlcipher.xcodeproj integration method for Community Edition*
SQLCipher for .NET, Xamarin, and Windows
- Client APIs now support a new sqlite-net compatible package based on the official praeclarum/sqlite-net library (was previously based on SQLite.Net-PCL) *
- Adds support for Microsoft Entity Framework via Microsoft.EntityFrameworkCore.Sqlite.Core 2.x
- Adds support for Microsoft’s ADO.NET implementation via Microsoft.Data.Sqlite.Core 2.x
- Substantial performance enhancements for Windows UAP and Runtime packages (up to 50%+ improvement under certain tests)
- Updates to all cryptographic support libraries including OpenSSL 1.1.1, OpenSSL 1.0.2p, OpenSSL FIPS 2.0.16, and LibTomCrypt 1.18.2
- Windows Phone is no longer supported due to the product end of life
Note: .NET, Windows and Xamarin packages are available exclusively via Commercial Edition packages and under the SQLCipher Enterprise Program.
Compatibility
Many of these changes provide a much higher level of security than previous versions of SQLCipher. However, the new page size of 4096, 256,000 KDF iterations, use of PBKDF2-HMAC-SHA512 and HMAC-SHA512 all modify important database settings. Thus, SQLCipher 4 will not open older databases by default. As always, we have updated our migration feature to streamline the upgrade process. To enable backwards-compatibility, it is possible to adjust settings at runtime or migrate older databases:
- To migrate and upgrade an existing database in place (preserving data and schema), use the new default settings, use PRAGMA cipher_migrate.
- To open an older database used pragmas to adjust settings back to their previous values. For example, to open a SQLCipher 3 database using SQLCipher 4, you could use the following statements after opening and keying the database:
PRAGMA cipher_page_size = 1024;
PRAGMA kdf_iter = 64000;
PRAGMA cipher_hmac_algorithm = HMAC_SHA1;
PRAGMA cipher_kdf_algorithm = PBKDF2_HMAC_SHA1;
- To attach and export data to a new database, use the sqlcipher_export() convenience function. This would let you control migration using very specific or custom settings.
Availability
Commercial Edition - On-demand access to new releases of SQLCipher Commercial Edition are available to licensees with an active CipherCare subscriber subscription, along with private, prioritized support directly from Zetetic. CipherCare subscribers will receive a separate email notification regarding the update and can contact us to request the latest SQLCipher distribution and applicable software license codes.
SQLCipher Enterprise Program - Enterprise Program Subscription customers will receive a separate email notification about the release, and the latest SQLCipher packages and license codes will be provided directly via your organization’s private online software delivery share.
Community Edition - SQLCipher 4.0.0 in source format is directly available on GitHub. The Community Edition of SQLCipher for Android is available via AAR packaging. The Community Edition of SQLCipher for iOS can be compiled from source or using CocoaPods.
Additional Details
Over the coming weeks we will be posting more detailed blog posts that elaborate on specific features and improvements that have been made with the latest SQLCipher release.
2018-11-01 08:00:00 -0400
Codebook Lite was originally introduced alongside Codebook to allow users a free option to try Codebook for iOS before they purchased. Now with the release of Codebook 3.6.0 we’ve introduced a 14-Day Free Trial option within Codebook. Because this functionality is now built into Codebook, we’re planning on discontinuing Codebook Lite development, so we can focus all our ongoing efforts on standard Codebook.
Similarly, standard Codebook has been a universal app (which works on both iPhone and iPad) now for a while and we’ve been phasing out Codebook for iPad (Legacy) for about a year, so we’re planning on pulling the plug at the same time as Codebook Lite.
Codebook Lite and Codebook for iPad Legacy will be fully removed from the App Store on January 1st, 2019. Please make sure to migrate your data to Codebook prior to this date or data loss could occur.
Migration Steps
Codebook Lite
Codebook for iPad Legacy
- Download the Codebook universal app
- Use the Codebook sync feature to sync your data from Codebook for iPad Legacy to a cloud service or a Desktop copy of Codebook.
- During the setup process for Codebook, you’ll be given the opportunity to use the sync feature to restore from the service or Desktop you synced with in step 2
- Once you’ve verified the data from Codebook for iPad legacy synced over to the new Codebook for iOS installation, feel free to delete the Codebook for iPad Legacy app