2026-04-28 08:00:00 -0400
We’re pleased to announce the immediate availability of SQLCipher 4.15.0. This release updates the SQLite baseline, addresses a defensive mode bypass in sqlcipher_export, updates cryptographic modules, and includes several other improvements.
SQLCipher Core
- Updates the upstream SQLite baseline to 3.53.0
- Sanitizes the source database name passed to
sqlcipher_export (reported by Dima Petschke from Deutsche Telekom Security GmbH)
- Improves error handling in
sqlcipher_extra_init
- Fixes the prototype for
sqlcipher_export_init
- Minor code cleanups
SQLCipher Commercial and Enterprise packages include the following enhancements:
- Updates OpenSSL-based cryptographic providers to 3.5.6 LTS
- Updates SQLCipher Enterprise FIPS Cryptographic Module
- Improves FIPS package support for iOS and Android targets in .NET MAUI
- SQLCipher for Java is updated to track the latest upstream release
- Improves SQLCipher for Android FIPS so that the FIPS module is extracted dynamically to allow more modern application packaging/bundling
SQLCipher for Android (all editions):
- SQLCipher for Android replaces internal Critical-based JNI APIs with non-critical equivalents to avoid stalls under heavy database usage
Defensive Mode Bypass in sqlcipher_export
The sqlcipher_export convenience function can be used to copy the contents of one attached database into another. It is most often used to convert between plaintext and encrypted databases. It needs to do dynamic schema manipulation, so the function temporarily clears defensive restrictions during operation. A vulnerability in the handling of the source database name parameter made it possible for a caller to supply a crafted source name, which could execute statements that defensive mode would otherwise block. This could allow direct modifications to the sqlite_schema table and database corruption. SQLCipher 4.15.0 now strictly validates the source database name and prevents the bypass.
This issue is assigned a CVSS 4.0 base score of 2.1 / Low (CVSS:4.0/AV:L/AC:L/AT:P/PR:N/UI:N/VC:N/VI:L/VA:L/SC:N/SI:N/SA:L). In order to practically exploit this issue, an application must already have an existing SQL injection vulnerability or allow unrestricted SQL access that reaches sqlcipher_export. Note that cryptographic integrity of the database is unaffected. Data remains encrypted under the application-controlled key at all times, all per-page HMAC and underlying integrity protections continue to function, and there is no leakage of data. Since the impact is bounded to schema-level modification, recovery may also be possible through restoration from backup, the SQLite recovery facility, or the correction of schema definitions.
Sincere thanks go to Dima Petschke from Deutsche Telekom Security GmbH for responsibly reporting this significant finding.
Cryptographic Provider Matrix
The table below summarizes the cryptographic providers used across SQLCipher packages and platforms:
| Edition |
Platform |
Cryptographic Provider |
| Community (non-FIPS) |
Android |
based on LibTomCrypt 1.18.2 |
| Community (non-FIPS) |
Apple |
Common Crypto (version varies by OS) |
| Commercial & Enterprise (non-FIPS) |
Apple |
Common Crypto (version varies by OS) |
| Commercial & Enterprise (non-FIPS) |
Other Platforms |
OpenSSL 3.5.6 LTS |
| Enterprise FIPS |
All Platforms |
SQLCipher Cryptographic Module
Based on OpenSSL 3.5.6 LTS |
Upgrading and Availability
SQLCipher 4.15.0 is available for download now, and we recommend that all applications upgrade to incorporate the sqlcipher_export fix and the other improvements in this release. As always, test your applications thoroughly with the new version before deploying to production.
Commercial and Enterprise - On-demand access to new releases of SQLCipher packages are available to all licensees with an active CipherCare support subscription from the Customer Downloads fulfillment site. Subscribers will also receive a separate email notification regarding the update and can contact us at any time for private support directly from the SQLCipher development team. Commercial and Enterprise edition upgrades require a new license code from the SQLCipher fulfillment site for each version. Don’t forget to change the license code in your application(s) when you upgrade.
Community Edition - SQLCipher Community Edition source code is available on GitHub, via AAR packaging for Android, and Swift Package Manager for Apple platforms.
For feedback and questions, please visit our Community Forum or private support channels. Thank you for using SQLCipher!
2026-03-17 08:00:00 -0400
We’re pleased to announce the immediate availability of SQLCipher 4.14.0. This release includes an important SQLite update, restoration of the LibTomCrypt cryptographic provider, and significant improvements for Android.
SQLCipher Core
- Updates the upstream SQLite baseline to 3.51.3, which fixes a critical WAL-reset database corruption bug. Applications running SQLCipher in WAL mode are strongly advised to upgrade.
- Reintroduces LibTomCrypt cryptographic provider support based on community feedback
- Updates the LibTomCrypt provider with improved logging and error handling
SQLCipher Commercial and Enterprise packages also include some important enhancements:
- Improves commit performance on Unix operating systems
- Updates OpenSSL-based cryptographic providers to use 3.5.5 LTS
LibTomCrypt Provider Restored
In response to community feedback, we have reversed the decision to remove the LibTomCrypt cryptographic provider that occurred in SQLCipher 4.12.0. LibTomCrypt is now included again with improved error handling and more detailed logging. It is also included as the default cryptographic module for one of our Community Edition packages, and may be used for others in the future.
SQLCipher for Android
SQLCipher for Android has undergone some major changes for this release:
- Adds Android consumer ProGuard rules to sqlcipher-android for default obfuscation settings
- Updates Room and androidx.sqlite API versions used with sqlcipher-android (now requires SDK version 23)
- SQLCipher for Android Community Edition now uses LibTomCrypt as its cryptographic provider
As noted above, the Community Edition of sqlcipher-android is now built with an updated LibTomCrypt 1.18.2. LibTomCrypt has already been used in long-term community builds by third parties for years. This change delivers some tangible benefits to the project:
- It is now possible to clone sqlcipher-android directly from GitHub and build it immediately for all targets. There are no additional steps required to build or obtain OpenSSL dependencies.
- It produces a smaller compiled artifact, reducing the footprint on applications.
- It addresses requests from the community for a simpler, more accessible open source build process.
- It provides a reduced surface area for false-positive security reports.
Commercial and Enterprise Android packages all continue to use OpenSSL (non-FIPS) or the SQLCipher Cryptographic Module (FIPS), unchanged.
SQLCipher for Windows UWP Deprecation
SQLCipher 4.14.0 is the last release that will include SQLCipher for Windows UWP packages for Commercial and Enterprise licensees.
For context, the SQLCipher for Windows UWP package is a specialized package that uses a WinRT sandbox. In the early days of the Microsoft Store, applications had to strictly adhere to the WinRT sandboxed API, so a special build of SQLCipher was required. However, that is no longer the case. The Microsoft Store relaxed requirements to accept standard Win32 and .NET applications in 2021, around the same time they officially deprecated UWP in favor of newer technologies like WinUI 3.
Given the deprecated state of UWP and WinRT, SQLite has signaled that WinRT API support will be completely removed in the next upstream release. This makes continued maintenance of a UWP-specific SQLCipher package impractical.
Since applications no longer need to use UWP or WinRT packaging to publish to the Store, it is possible for applications using SQLCipher to move to the official SQLCipher for Windows .NET package. All Commercial and Enterprise licensees with an active subscription for SQLCipher for Windows UWP will automatically receive a transfer license which can be used as a drop-in replacement. Code changes shouldn’t be required for applications that are not using UWP-specific APIs. Licensees will be contacted separately with transfer license details prior to the next SQLCipher release.
Cryptographic Provider Matrix
The table below summarizes the cryptographic providers used across SQLCipher packages and platforms:
| Edition |
Platform |
Cryptographic Provider |
| Community (non-FIPS) |
Android |
based on LibTomCrypt 1.18.2 |
| Community (non-FIPS) |
Apple |
Common Crypto (version varies by OS) |
| Commercial & Enterprise (non-FIPS) |
Apple |
Common Crypto (version varies by OS) |
| Commercial & Enterprise (non-FIPS) |
Other Platforms |
OpenSSL 3.5.5 LTS |
| Enterprise FIPS |
All Platforms |
SQLCipher Cryptographic Module
Based on OpenSSL 3.5.5 LTS |
Upgrading and Availability
SQLCipher 4.14.0 is available for download now. We recommend testing your applications thoroughly with the new version before deploying to production.
Commercial and Enterprise - On-demand access to new releases of SQLCipher packages are available to all licensees with an active CipherCare support subscription from the Customer Downloads fulfillment site. Subscribers will also receive a separate email notification regarding the update and can contact us at any time for private support directly from the SQLCipher development team. Commercial and Enterprise edition upgrades require a new license code from the SQLCipher fulfillment site for each version. Don’t forget to change the license code in your application(s) when you upgrade.
Community Edition - SQLCipher Community Edition source code is available on GitHub, via AAR packaging for Android, and Swift Package Manager for Apple platforms.
For feedback and questions, please visit our Community Forum or private support channels. Thank you for using SQLCipher!
2026-03-16 08:00:00 -0400
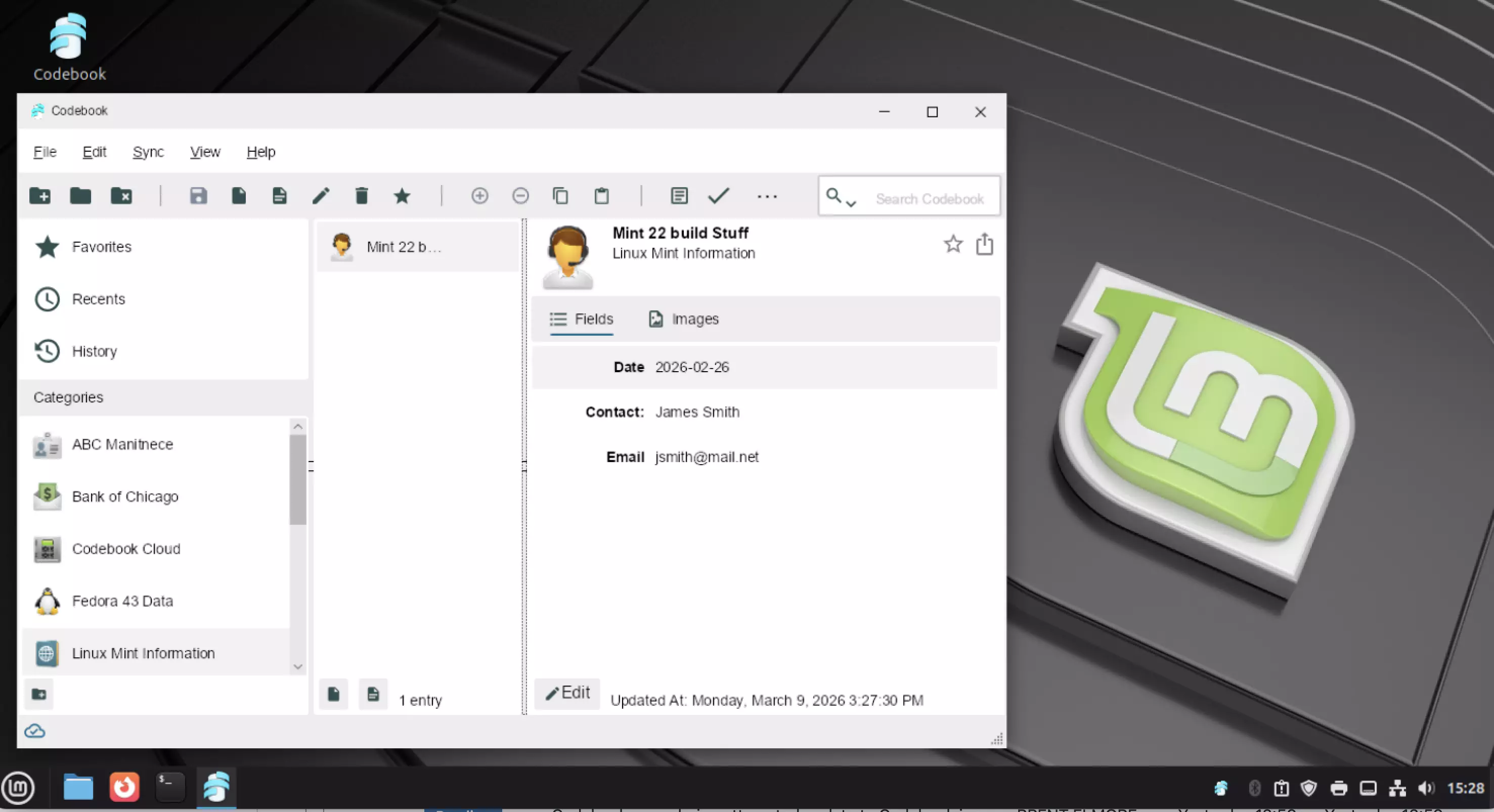
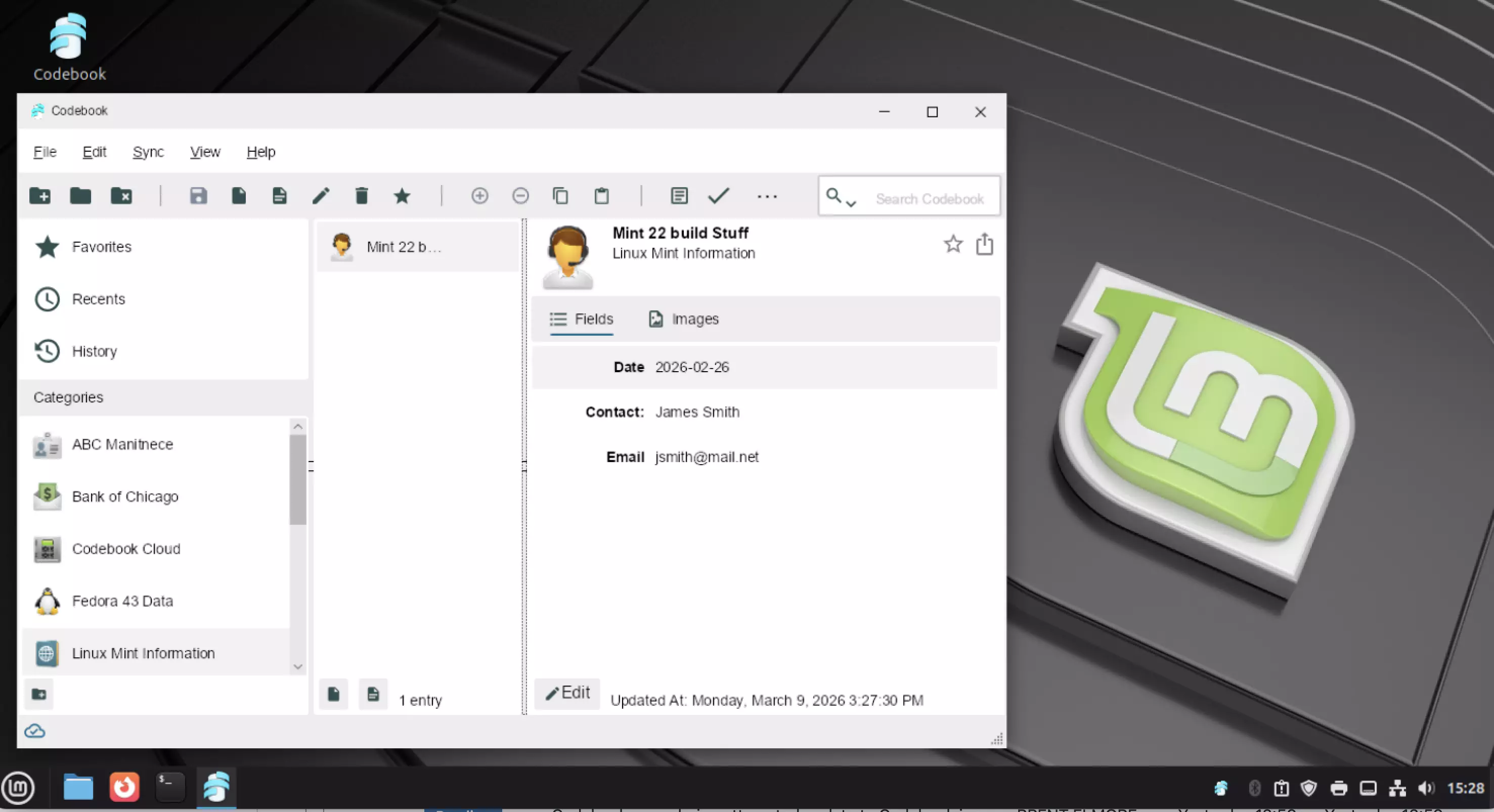
A number of customers have inquired about accessing their Codebook data on the Linux platform over the years. Recently, there’s been an uptick in interest in Linux, potentially driven by Microsoft ending support for Windows 10 late last year. Windows 11 has certain hardware requirements which may prevent some users from updating.
With the release of Codebook for Windows 5.3.10 we’re happy to announce that Codebook for Windows runs seamlessly on Linux through Wine. Wine is an open-source compatibility layer allowing Windows applications to operate on Linux. This release includes compatibility adjustments for Codebook when running on Linux. There are a few limitations currently, which we’ve identified here.
If Linux is a new operating system for you, you may be concerned about a new environment. Over the years, new distributions (variations of Linux) have been released, many which provide a polished user experience, especially those migrating from other operating systems. If you’re unsure about which distribution to try, we’ve found Linux Mint to provide a great end-user experience when running Codebook. If you prefer a different distribution, Codebook will also run on Debian/Ubuntu, Red Hat, and Fedora distributions.
How do you get started though? We’ve put together a script which can be run within your Linux terminal to install Wine, the necessary prerequisites, and Codebook itself. We’re happy to have Codebook working with Tux 🐧. Give it a try, the script below will do the work, we’d love to hear your feedback!
curl -s https://www.zetetic.net/downloads/codebook/windows/codebook-wine.bash | bash
2026-01-20 07:00:00 -0500
We’re pleased to announce the immediate availability of SQLCipher 4.13.0. This is a minor maintenance release that updates the SQLite baseline and addresses a couple of small fixes in core and packaging.
SQLCipher Core
- Updates the upstream SQLite baseline to 3.51.2
- Corrects encoding for
sqlcipher_export() function registration
- Copies dSYMs and includes them in Apple package xcframeworks
Upgrading and Availability
SQLCipher 4.13.0 is available for download now. We recommend testing your applications thoroughly with the new version before deploying to production.
Commercial and Enterprise - On-demand access to new releases of SQLCipher packages are available to all licensees with an active CipherCare support subscription from the Customer Downloads fulfillment site. Subscribers will also receive a separate email notification regarding the update and can contact us at any time for private support directly from the SQLCipher development team. Commercial and Enterprise edition upgrades require a new license code from the SQLCipher fulfillment site for each version. Don’t forget to change the license code in your application(s) when you upgrade.
Community Edition - SQLCipher Community Edition source code is available on GitHub, via AAR packaging for Android, and Swift Package Manager for Apple platforms.
For feedback and questions, please visit our Community Forum or private support channels. Thank you for using SQLCipher!
2026-01-05 19:00:00 -0500
Today we are very excited to announce the release of the new Secure Sharing feature for Codebook Cloud, available in the latest updates for all platforms in the 5.3 release series. We are also making available new Family Plan subscriptions, to support multi-user accounts.
This is a feature that has been frequently requested for a long time, and it's built on top of the Codebook Cloud sync service.
Secure Sharing
Version 5.3.x
Secure Sharing allows you to share an entry record, including all its fields and attachments, with another Codebook Cloud user. Tap or click on the new Share Entry button on any entry record to get started.

You can share entries directly with other users within your account, or request to share with Codebook Cloud users who have their own accounts. Secure Sharing uses the state-of-the-art, post-quantum cryptography algorithms ML-KEM and ML-DSA for protecting your data. Learn more about how these are used here.
This new feature requires a Codebook Cloud account. It is not something we could have added to the older sync services, as it requires a coordinating server.
Family Plans
Multi-user accounts at a discount
The new Family Plan subscriptions are available on all platforms that we
support, billed monthly or annually, and allow for up to six users including
the account owner.
We have a special discount for new subscribers: sign up for a Family Plan now for 25% off the first year. Use the link below to create a new Codebook Cloud account with this discount.
25% Off for New Subscribers
Offer unavailable in Google Play or Apple App Store.
Offer expires Jan 31st.
If you already have a Codebook Cloud subscription and would like to upgrade to a Family Plan, you can Manage Your Subscription.