We are excited to announce the beta availability of a new version of SQLCipher For Android. This new release provides major benefits including optimized support for concurrent database access, drastic performance improvements, API simplification, and codebase modernization. With the new library SQL operations are executed on a ThreadLocal<SQLiteSession> instance which completely eliminates the aggressive locking behavior that could occur with the original version of SQLCipher For Android. Built-in WAL journal mode and connection pooling allows for parallel execution of queries from multiple threads. The updated Java API, based on the android.database package found in the AndroidBindings project, eliminates virtually all dated legacy code from the project.
History
We would like to thank Signal for helping to support the development of this new library which will benefit Android developers everywhere. SQLCipher For Android was initially released over 10 years ago following initial work with Guardian Project, making the security provided by SQLCipher available on the Android ecosystem. A lot has changed over the years; Zetetic continues to maintain the library, integrating new versions of SQLCipher, adding support for 64-bit device architectures, adding Room/Support API integration (thanks commonsguy!), and improving the project integration experience to name a few. SQLCipher For Android was based on an older version of the android.database.sqlite Java API. Unfortunately, this limited the abilities of the library, specifically in terms of concurrency. The new version of the library builds on the solid foundation of SQLCipher for Android with an eye toward concurrency at the forefront.
Availability
As SQLCipher for Android receives downloads in the hundreds of thousands every year, we are taking a safe and measured approach to revising the library; providing stability for developers who depend on the security of SQLCipher is paramount. Zetetic will continue to maintain the original SQLCipher For Android library for some time until the refresh may be considered a full replacement. Initially, the new library will be available in source-only format (available here); developers will need to provide both the SQLCipher amalgamation and OpenSSL dependencies to evaluate the library while we are in a preview state. Eventually, we will publish Community edition AAR artifacts. Commercial and Enterprise SQLCipher customers may access prerelease builds of the new SQLCipher for Android library from the Customer Downloads fulfillment site. While we are releasing the software in preview mode for now, the library is fairly stable and is already in use in on millions of devices with great success.
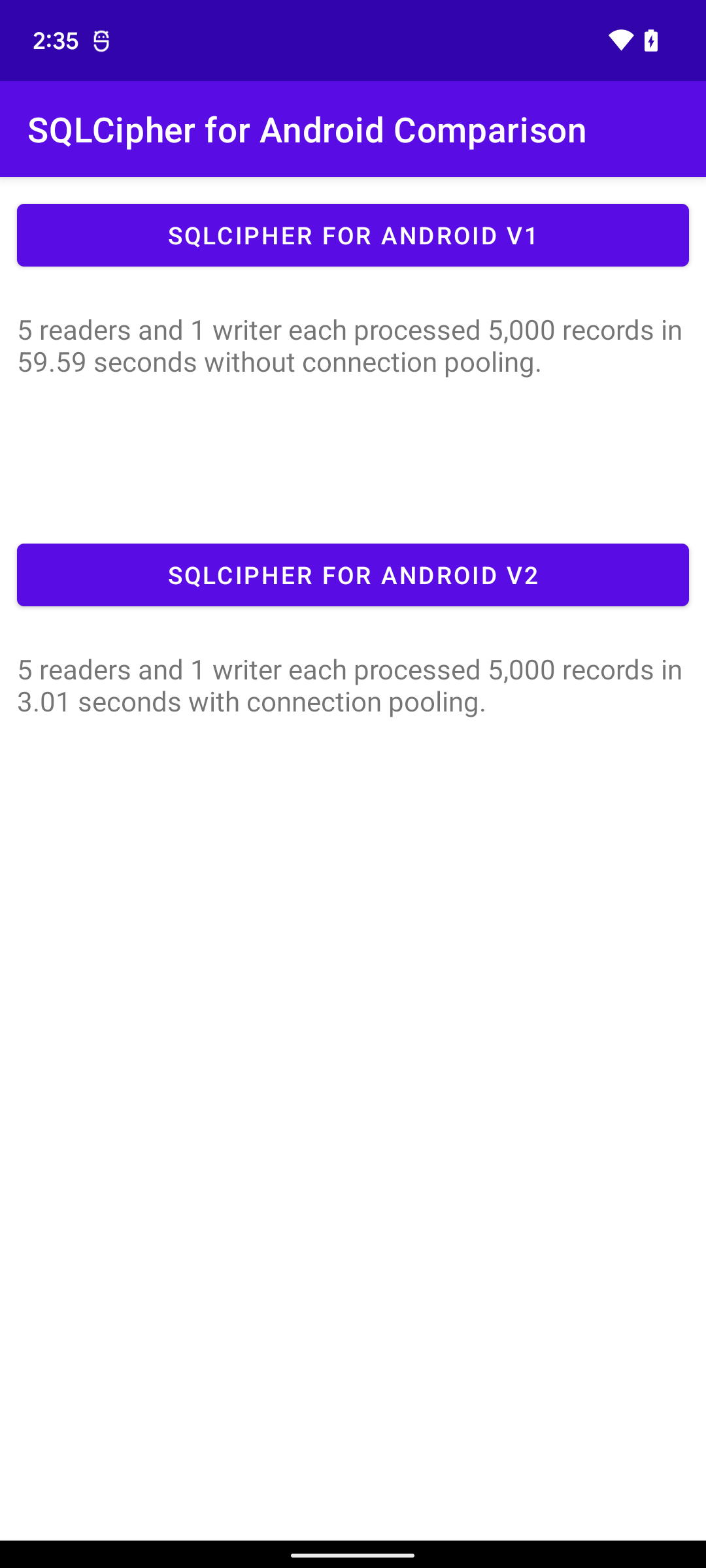
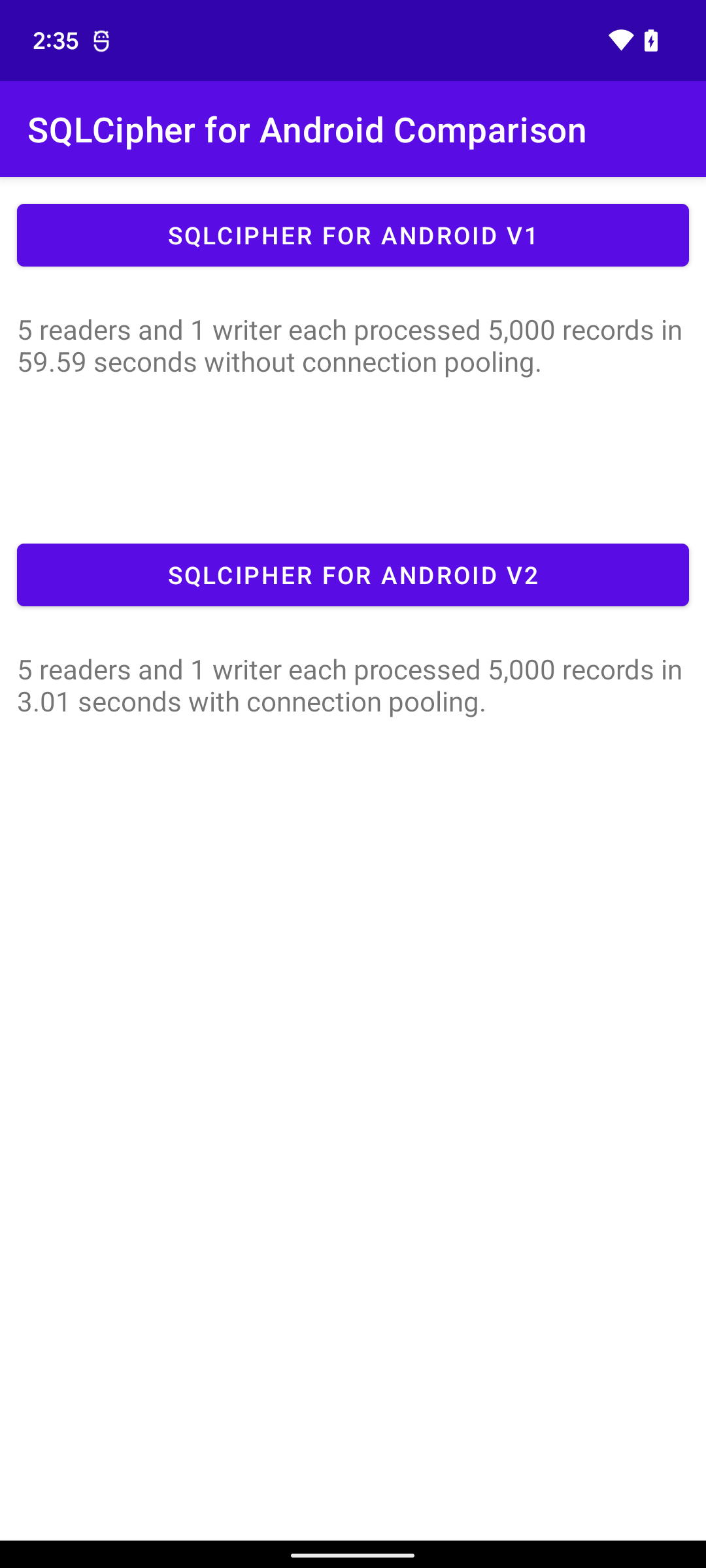
To provide some context around the performance difference between the old and new versions of SQLCipher for Android we prepared a small application that bundles both versions of the library and performs a series of multithreaded operations. The scenario represents a single writer operation producing 5,000 records. Concurrently, we have 5 separate reader operations running in separate threads attempting to individually read all data produced by the writer. The old (current) version of SQLCipher for Android took 59.59 seconds to process all records on a Pixel 6 device. The new version was able to complete the same task in 3.01 seconds. We look forward to hearing your feedback regarding the new library as we prepare to continue our support of SQLCipher for Android in the future.
We are pleased to announce that SQLCipher 4.5.1 is now available. It includes the following major changes:
SQLCipher Core
- Updates baseline to use SQLite 3.37.2. IMPORTANT: This version includes an upstream SQLite fix for a database corruption bug. The bug could cause corruption when using
SAVEPOINT operations. We recommend any applications using SAVEPOINT upgrade to the latest release.
- Adds new
PRAGMA cipher_log and cipher_log_level features to allow logging of TRACE, DEBUG, INFO, WARN, and ERROR messages to stdout, stderr, file, or logcat
- Modifies
PRAGMA cipher_profile to use sqlite3_trace_v2 and adds a logcat target for Android
- Updates OpenSSL provider to support the
EVP_MAC API with version 3+
- Allows
PRAGMA cipher_integrity_check to work properly with databases larger than 2GB
- Fixes a missing munlock-before-free bug causing issues on some platforms
SQLCipher Commercial and Enterprise
The following changes and enhancements are available for Commercial and Enterprise packages:
- Significant optimizations to improve performance on all platforms
- Fixed issue that could cause excessively slow operation on Android emulators when using fast-boot
- Statistics collection is now disabled by default, but can be enabled with
PRAGMA cipher_stat_memory = ON and PRAGMA cipher_stat_crypto = ON.
- Java and .NET library wrappers have been updated to the latest available versions.
- non-FIPS packages using OpenSSL now include the latest release of 1.1.1m.
Availability
Commercial and Enterprise - On-demand access to new releases of SQLCipher packages are available to all licensees with an active support subscription from the Customer Downloads fulfillment site. Licensees will also receive a separate email notification regarding the update and can contact us at any time for private support directly from the SQLCipher development team.
Community Edition - SQLCipher Community Edition source code is available on GitHub, via AAR packaging for Android, and CocoaPods for iOS.
Time for another Codebook development update post, over on the discussion forum! We’ve spent the last few days of the year working on some long-requested, nice-to-have improvements for Codebook for Windows and Codebook for iOS, check out the post for demo videos, and please let us know what you think!
We are pleased to announce that SQLCipher 4.5.0 is now available. It includes the following important changes:
SQLCipher Core
- Updates baseline to use SQLite 3.36.0
- Changes the enhanced memory security feature to be DISABLED by default; once enabled by
PRAGMA cipher_memory_security = ON, it can’t be turned off for the lifetime of the process
- Changes
PRAGMA cipher_migrate to permanently enter an error state if a migration fails
- Fixes memory locking/unlocking issue with
realloc implementation on hardened runtimes when memory security is enabled
- Fixes
cipher_migrate to cleanup the temporary database if a migration fails
- Removes logging of non-string pointers when compiling with trace level logging
Important Upgrade Considerations
SQLCipher 4.5.0 contains two important changes that alter the fundamental behavior of SQLCipher.
Memory Security: SQLCipher 4.0 introduced a new enhanced memory security feature. While SQLCipher had previously implemented memory sanitization and locking for internal allocations related directly to SQLCipher’s cryptographic implementation, the new memory security feature extended to ALL memory allocated by the library (i.e. by SQLite internal logic outside of SQLCipher). Initially this feature was enabled by default. However, after reviewing feedback from customers and the community, we have decided to disable this feature by default, but still allow it to be enabled on demand. This will allow developers to selectively turn on this feature when dictated by their security requirements without impacting performance for all use cases. Note that if your application requires the memory security feature, it must call PRAGMA cipher_memory_security = ON early in the application life-cycle to enable the feature. Once memory security is enabled it can’t be disabled for the lifetime of the process.
Migration: Previous versions of SQLCipher’s PRAGMA cipher_migrate could leave a database connection usable after a failed upgrade. While an error would be reported in the result set, if an application ignored the return it could continue to use the database at the older version’s security setting. The most common cause of this issue would be inadequate drive space to perform the migration or an attempt to migrate on a read only connection. In SQLCipher 4.5.0 the database connection will be rendered unusable (causing an exception to be thrown or a hard error reported). Applications that use cipher_migrate and upgrade to 4.5.0 should ensure they check the result set from the PRAGMA and handle any migration exceptions.
SQLCipher Commercial and Enterprise
The following changes and enhancements are available for Commercial and Enterprise packages:
- The SQLCipher Statistics feature now includes detailed memory usage information. The
sqlcipher_stats virtual table will now return current library memory use, high memory use, memory allocation, reallocation, and free times and counts. These statistics are inclusive of memory sanitization time, allowing for detailed profiling of the enhanced memory security feature.
- Packages now use in-memory temporary storage by default, but allow an application to override that setting using
PRAGMA temp_store = FILE;. Using FILE temporary storage may be necessary in certain circumstances, like performing a VACUUM on a very large database.
- SQLite’s snapshot feature is now enabled.
- Java and .NET library wrappers have been updated to the latest available versions.
- non-FIPS packages using OpenSSL now include the latest release of 1.1.1l.
SQLCipher for Android Refresh Upcoming
Zetetic is actively developing a new SQLCipher for Android library that is completely rebuilt with an updated Java API, more closely tied to the current Android android.database.sqlite implementation. This new library is seprate from, and being developed in parallel with, the current SQLCipher For Android library. It natively supports connection pooling and other advanced features providing vastly improved performance, concurrency, and developer experience.
This new SQLCipher for Android will initially be available on GitHub and will require developer build integration for dependencies. Community and Commercial build artifacts will be available once we begin to transition to the new library after thorough testing. The existing SQLCipher for Android packages (android-database-sqlcipher) will continue to be maintained in parallel during a transition period, before the old library is eventually deprecated. Keep an eye out for future details about the availability of the new library!
Availability
Commercial and Enterprise - On-demand access to new releases of SQLCipher packages are available to all licensees with an active support subscription from the Customer Downloads fulfillment site. Licensees will also receive a separate email notification regarding the update and can contact us at any time for private support directly from the SQLCipher development team.
Community Edition - SQLCipher Community Edition source code is available on GitHub, via AAR packaging for Android, and CocoaPods for iOS.
Codebook 4.4, the latest release of our password manager, is now available. In this version we’ve added support for storing image and PDF files as attachments to Entry records, along with support for large databases (e.g. > 1GB), an improved sync feature, and a ton of other adjustments and improvements. A new Help page is available for the attachments feature, and we’ve got a getting started tutorial for it as well. Get the full run-down of changes in this version, and update to the latest version to check it out!