2013-04-26 11:03:19 -0400
We are planning to gather a group of users to participate in a private beta of SQLCipher for Android. We are looking for individuals who already have some experience integrating SQLCipher for Android into their application and have an interest how the library evolves in the future. This group will have access to new builds of SQLCipher for Android along with private communications with Zetetic to provide feedback as changes are made.
We have recently been in discussion with members of the Android development team at Google where they have been helpful in testing out some changes to SQLCipher for Android on an upcoming Android platform release. While this is very benefitial, we would like to reach out to the community to further understand how changes to the library may impact you in the future.
If you are interested in helping SQLCipher for Android evolve in the future, and are willing to actively test, provide feedback on new builds, and contribute test cases, you can contact us to be considered for the private beta. Please send emails to support@zetetic.net and include a bit of inforomation about your app and how you currently use SQLCipher in your request. Thanks!
2013-04-08 10:57:08 -0400
Update: STRIP 2.0.0 for OS X has been released. Upgrade instructions can be found here.
We've been posting the last few beta update notices for the STRIP 2 for OS X beta here so we have a handy place to refer to the update. If you're not part of the beta test, please ignore this post. If you would like to help us beta test in the future, please write us at support@zetetic.net. We don't have any open slots at the moment, but we always need new folks to help and will gladly add you to the list!
This should be the final test version of STRIP 2 for OS X, barring any show-stoppers, so please give it a good shake. The version number is 1.3.0b6, it's the third and hopefully final release candidate we've done (I know, we've been testing for a long time).
Some re-arrangement has happened with the Sync menu, Preferences, and there's a secret new sync feature we're looking forward to announcing on release day. We're going to submit this one to the Mac App Store for review soon, so we might be able to do the official release in a month (our review times for STRIP for OS X have been over 30 days in the past so we'll have to see). If you see anything askew, please write us at support@zetetic.net.
One more thing—we've been going through the apps and correcting use of "Strip" to the capitalized STRIP, including dialogs, the application name itself, etc. If you see any that we missed, please let us know.
Updated versions of STRIP for iPhone and STRIP for iPad are on the way to beta testers registered with our TestFlight service, please check your email or get in touch with us if you didn't get the notice.
Thanks everyone for all your help, we're really excited about this release!
2013-02-20 09:47:39 -0500
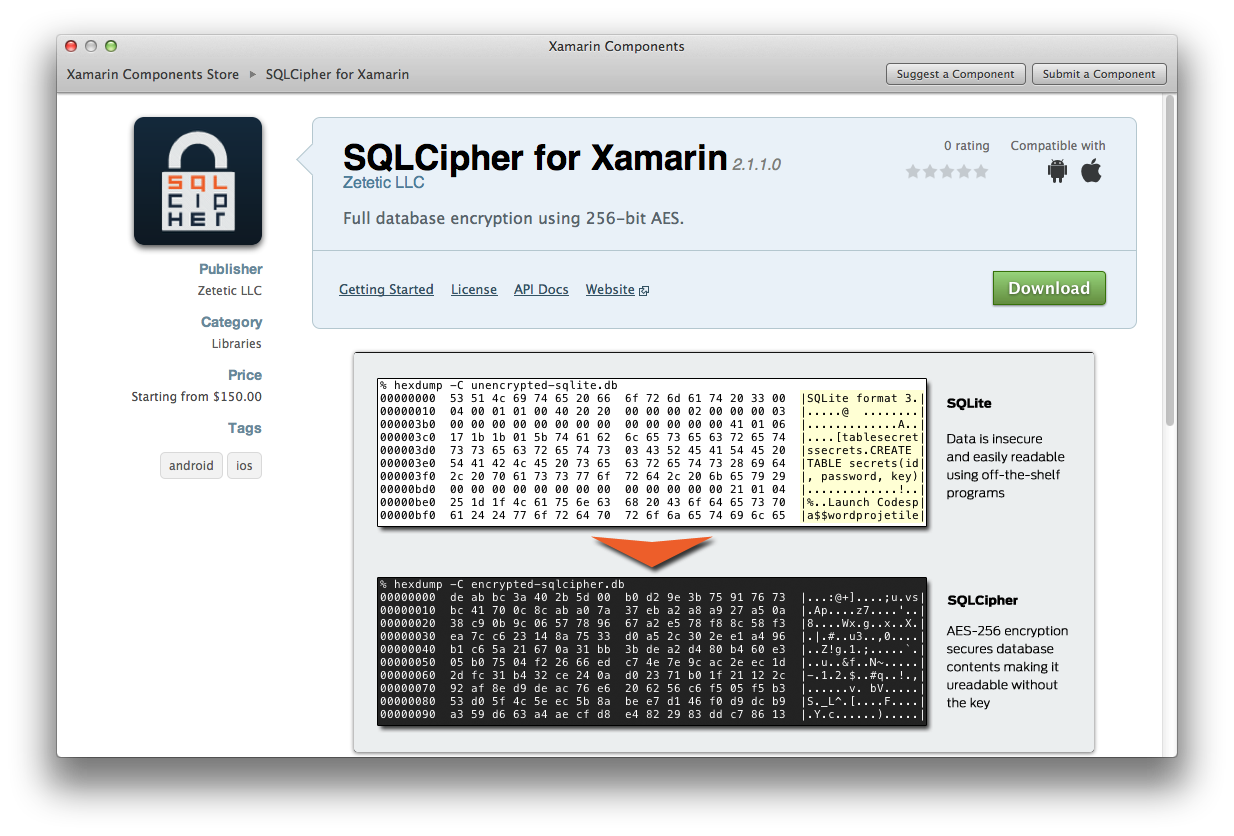
We're pleased to announce that we've partnered with Xamarin to make SQLCipher available directly from Xamarin's new Component Store.
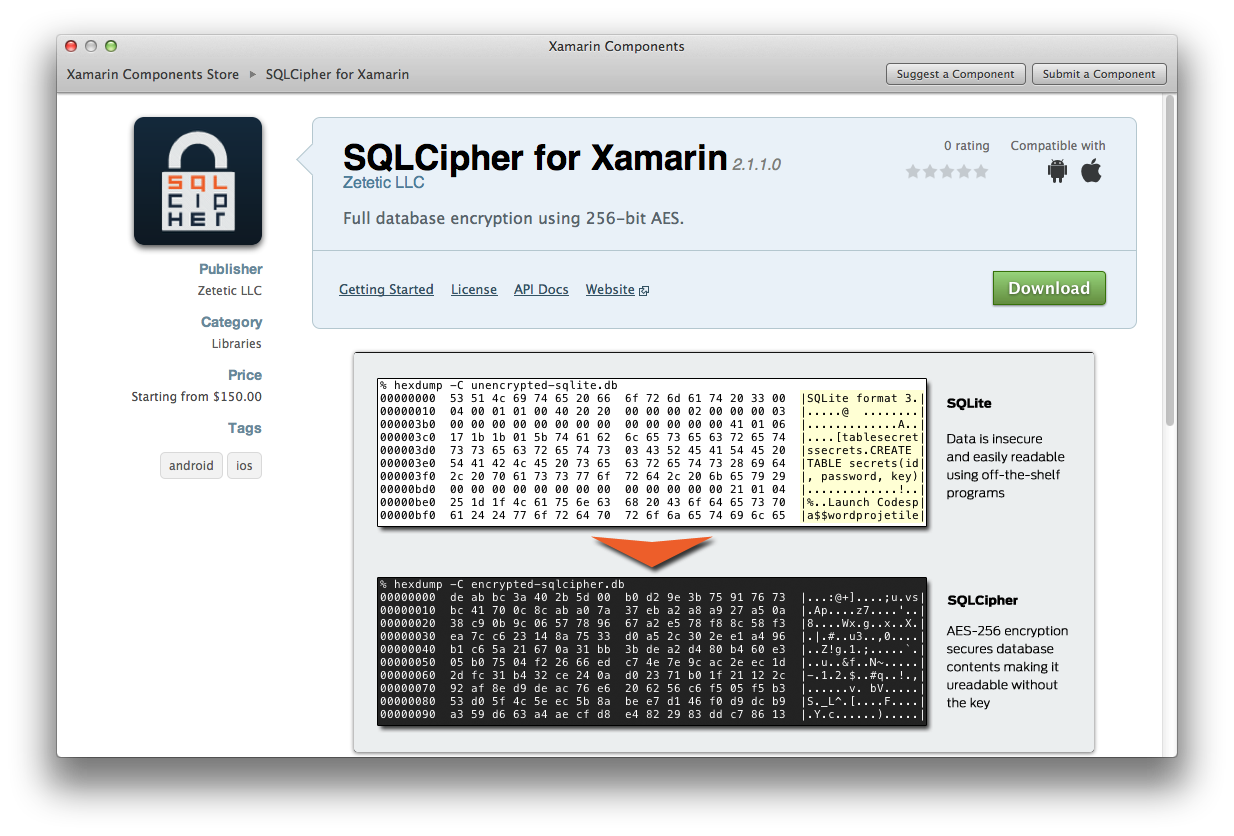
Developers using the new Xamarin Studio can now easily install SQLCipher (and other 3rd party libraries) through the component store. There are no longer additional steps for packaging native .so libraries for Android and we've eliminated the configurations for linking static archives on iOS. Everything is bundled into a single library and automatically configured in your application project, making secure database integration using C# on Android and iOS quick and painless.
Please check it out and let us know what you think!
2013-02-19 15:04:15 -0500
We'll be posting the last few beta update notices for the STRIP 2 for OS X beta here so we have a handy place to refer to the update. If you're not part of the beta test, please ignore this post. If you would like to help us beta test in the future, please write us at support@zetetic.net. We don't have any open slots at the moment, but we always need new folks to help and will add you to the list.
1.3.0b5 Release Notes
Note: This release includes a database update which requires you to update your other copies of STRIP as well to maintain sync compability. Click here to download this release directly. Only registered beta testers with a license from us can run this build, please don't download it if that's not the case for you.
- Disables "Install & Relaunch" due to incompatibility with OS X Sandbox
- Updates sync service to support non-ascii UTF-8 characters in password during HMAC authenticaiton
- 50 new icons to supplement the current set
- Fix crash on edit
As always, if you have any issues, please email us at support@zetetic.net.
Note: if an issue you've already reported isn't mentioned above, we're still working on it. Thanks!
2013-01-21 11:30:07 -0500
Many of us here at Zetetic use Homebrew, a command-line tool used to build and manage various software packages on OS X. Currently there are over 2200 recipes available to be installed via Homebrew. While building SQLCipher is not difficult, installing from Homebrew is just as easy and also affords you the ability to easily upgrade your installations as updates are released, all managed within a central location. We have submitted a recipe for SQLCipher that is now available to the masses. If you already have Homebrew installed, you will want to update your current list of recipes:
brew update
To install our current release, simply run:
brew install sqlcipher
If you wish to run the bleeding edge of SQLCipher, you can request the install perform a build from our master branch:
brew install sqlcipher --HEAD
This will install what is called a keg-only package of SQLCipher to minimize conflicts with other dependencies on SQLite due to the shared binary name. In order to make SQLCipher available on your PATH you can run:
brew link sqlcipher --force
Happy brewing!