Google has just published a serious new web vulnerability, POODLE, affecting SSL 3.0. Because this flaw that can leak data, and compromise user and system security, we have disabled SSL 3.0 for our sites and services, including zetetic.net and Tempo. Unfortunately there is no other viable workaround at this time.
Please note that this should not affect the vast majority of users running on modern supported browsers, however IE 6 on Windows XP will no longer be able to connect to these sites. Please feel free to contact us if you have an questions or concerns.
As noted on our community discussion site, there’s an update to STRIP for iPhone and STRIP for iPad out today in the iTunes App Store that addresses a couple of recent issues. Version 2.4.2 should start showing up in the iTunes App Store soon if you don’t see it just yet.
The latest release of SQLCipher, version 3.2.0 which is based on the stable upstream release of SQLite 3.8.6 is now available. With this release, we would like to highlight a few specific changes that were introduced. First, a new PRAGMA, cipher_store_pass which allows for the source passphrase to be stored in RAM, even after key derivation. Typically the source passphrase is zeroed from memory once a key is computed. Now, if PRAGMA cipher_store_pass is set, operations such as an ATTACH database command will used the passphrase stored in memory, thus the requirement to provide a KEY value are not needed unless a different value is required for the key. Note, PRAGMA cipher_store_pass is disabled by default and the memory is locked when supported on the given platform to prevent the memory from being paged into a swap file. When PRAGMA cipher_store_pass is enabled, the stored passphrase is wiped when the database is closed.
In this release we are happy to announce commercial support of SQLCipher on Windows Phone 8.1. Finally, we have included a fix to the Common Crypto provider in which key derivation was occurring twice, this should reduce the first operation requiring KDF by 50%. SQLCipher for Android has been validaed on Android platforms 2.1 through Android L preview. Commercial builds for all supported platforms are available immediately. We are aware of the forthcoming SQLite 3.8.7 release, which promises to be up to 50% faster. We are planning to incorporate 3.8.7 in a follow-up release once it has been released and stabilized. We look forward to hearing your feedback with the latest release, please get in contact!
Just a quick announcement here that we’re releasing 2.4.2 of STRIP for OS X to address some issues introduced in 2.4.0 alongside the new Secret Agent feature and other bugs. Main highlights: we added a keyboard shortcut preference for Secret Agent so you can set what you like (the default of shift+command+\ doesn’t work on many keyboards turns out), and we restored the old height of the rows in the Categories and Entries list.
Changes in this version:
- New keyboard shortcut preference added for Secret Agent on the Preferences window
- Changes keyboard shortcut for Lock to shift+command+L
- Adjusts tab control loop on main window
- Switches height of categories and entries lists back to system default by popular demand
- Fixes various memory leaks
- Ensures New Feature Tour window is visible on smaller screens and resizable
- Updates Secret Agent to allow for use in full screen apps
Many users interact with SQLCipher encrypted databases outside of application code for testing, database development, or troubleshooting. Yet until recently, we’ve only been able to recommend the use of the SQLCipher’s command line shell that is included in many of the SQLCipher Commercial Edition packages, or compiled under Community Edition distributions.
While powerful, many would prefer the experience of a native, graphical, desktop application instead of a command line shell tool, and we frequently receive inquiries about GUI tools that support SQLCipher.
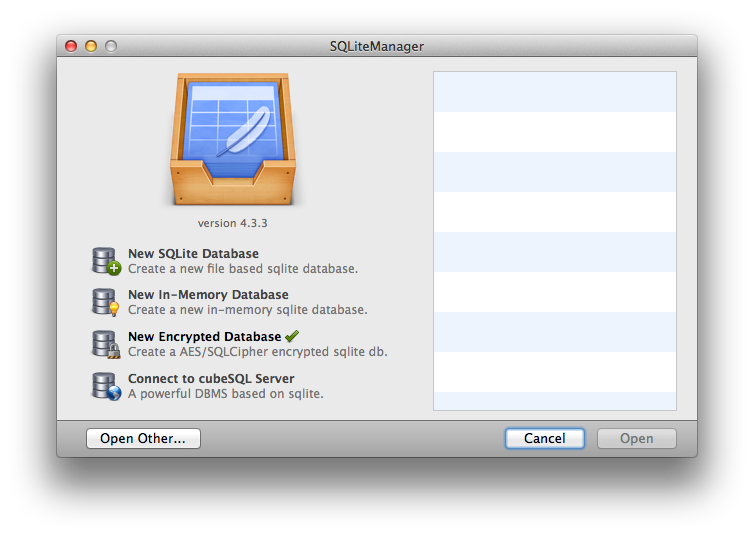
For this reason, we are now very happy to announce that SQLiteManager, a popular and feature-rich database management studio from SQLabs, has released version 4.3.3 that adds native support for SQLCipher encrypted databases.
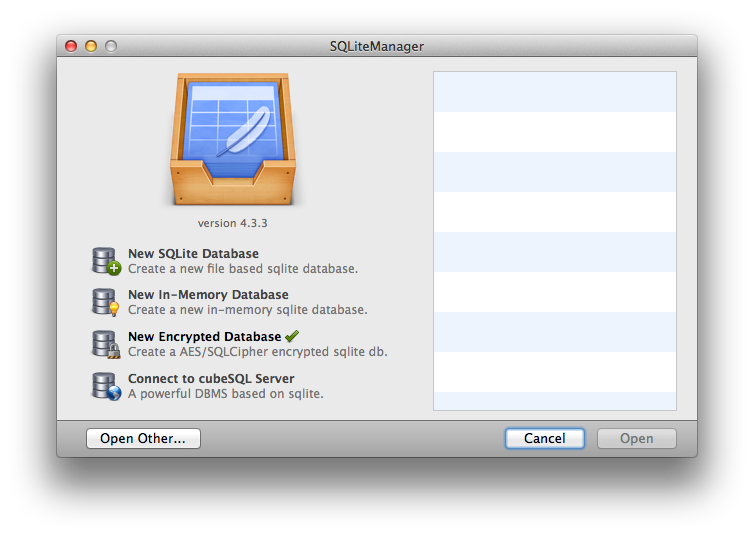
SQLiteManager provides a suite of advanced features for SQLCipher database management, including:
- Query execution
- Inline editing with syntax highlighting
- Table / schema editing
- Graphs and Charting
- Data import/export functions
- Support for both Windows and OS X.
If you need a user friendly and graphical interface for SQLCipher, please check out SQLiteManager today. Best of all, when you purchase SQLiteManager using the button below, you will help support the ongoing development of the SQLCipher project!
Buy SQLiteManager »