2018-03-22 07:00:00 -0400

Last week two of our developers, Micah Moore and Billy Gray, attended Teki Con, a three-day, single-track iOS development conference in Atlanta, Georgia hosted by Catamaran, LLC. Getting into WWDC can be tough these days so we’ve had our eye out for a focused and advanced discussion of iOS development and we sure got it! Among the speakers were a number of developers we already follow, and some seriously big names discussing application architecture and code design (did you know MVC stands for “Massive View Controller”? 😜). There were also quite a few speaking who were new to us and taught us a lot. Every session was fantastic, whether it was on the trials and travails of running a viral app, category theory (“a monad is just a monoid in the category of endofunctors”), accessibility, developer tools and debugging, or philosophy and approaches to common development patterns.
The tiki theme of the event wasn’t just a name—it kicked off with a wonderful hula dance performance and Mike Lee’s talk, “We’re Doing It Wrong,” which was chockfull of interesting facts about Hawai’i and how its culture evolved over time in his discussion of how we can better approach our work and the world around us.
Many of the speakers, including Michael Ayers, Krzysztof Zabłocki, and Dave DeLong (yep, a UIKit engineer!) focused on app architecture, in particular on coordinators and composition, as well as diving into how to use either delegation or dependency injection to keep an app true to its design pattern, whether that’s MVC or MVVM.
Among the more elucidating observations was perhaps the nut of Dave DeLong’s talk:
“UIViewController is not a controller, it’s a view!”
He put this gif up on his slide right then, it ably demonstrates the profound affect this had on us. The name of this UIKit component has tended to suggest we use it in a way we should not, and over the years the documentation from Apple has also suggested it, creating a perceived conflict between what’s being advised and staying faithful to an MVC or MVVM design pattern. This perspective frees us from some concerns that have made us wary of experimentation.
The third day of the conference was set aside for labs, two awesome workshops run by Big Nerd Ranch. We had the choice between labs on advanced auto layout and advanced iOS performance; we chose the latter as it was of particular interest for some new things we are looking into. The lab was an abbreviated form of BNR’s day-long training classes on the same topic, and included a course book in PDF form along with before-and-after Xcode projects for each of the problems we worked on. The course instructors did a great job taking us though advanced uses of operation queues, Grand Central Dispatch, and layer transformations and animations. It was a bit of a crash course for both of us in Swift (we’re still new to the language, we seemed to be among the few primarily obj-c attendees who understand retain/release and what a zombie object is!) but it was quite a lot of fun and pretty easy for us to follow along.
Long story short: we highly recommend attending Teki Con assuming they hold it again next year! Kudos to Jonathan Crockett and Stephen Elliot for putting together such a great speaker line-up and conference.
2017-12-22 07:00:00 -0500
We are happy to announce SQLCipher 3.4.2 has been released. This release includes integration of the upstream SQLite release 3.20.1. Along with the many improvements included in SQLite, several of our client libraries included some nice additions with this release.
More details and instructions for accessing the latest version can be found in our official release announcement here.
2017-12-20 07:00:00 -0500
We’ve got some exciting news for customers of our password manager Codebook, just in time for the end-of-year holidays: a complete redesign of the app’s embedded database icons along with fifty new ones, expanding the set to 200! They are available now on all four platforms: Android, iOS, macOS, and Windows.
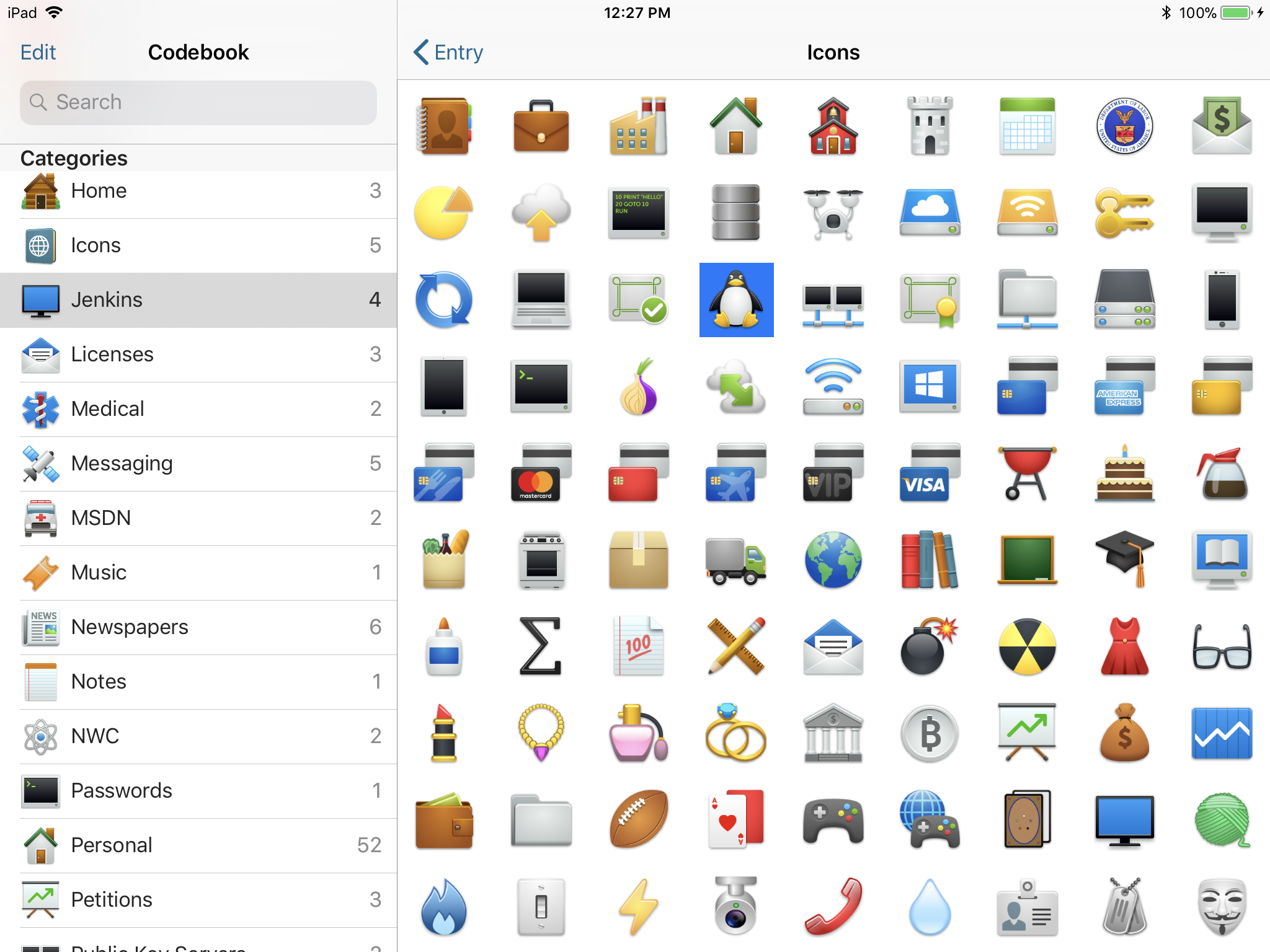
To get it done we worked with Icon Factory, whose work you may have seen around, and they really delivered on both the style updates and the new additions to the set. This is a big deal for us as it’s not something we can do often, and these icons tend to make up quite a bit of the interface of Codebook once it’s been populated with records.
For the new icons we drew in part from the many requests we’ve received over the last few years directly through our support mail account and in response to requests for comment on our discussion forum. We really appreciated all that input and welcome more, so if we’re missing something you’d like to see added, let us know, we do keep a list.
For the new style we wanted to go with a more business-friendly look that maintained the charisma and humor of the current set, with more depth and details to take advantage of today’s high-resolution displays. We hope you’ll agree that the result is impressive:
| Before |
After |
Before |
After |
 |
 |
 |
 |
 |
 |
 |
 |
 |
 |
 |
 |
 |
 |
 |
 |
 |
 |
 |
 |
All the existing icons got updated to the new style should be recognizable, but we did repurpose one of the–three!–phone-related icons to something for the shortwave or radio enthusiast:
As to the new icons, here’s a pseudo-random sampling:
| Programming |
CI / Dev Ops |
Security Certificate |
GPG / Keypair |
 |
 |
 |
 |
| Amazon |
Home Security |
TOR |
Payroll |
 |
 |
 |
 |
| Rail |
Transit Card |
Outdoor Sports |
Healthcare.gov |
 |
 |
 |
 |
It was a pleasure to work with Icon Factory on this project, many thanks to them for a job well done. Enjoy the new icons, and Happy Holidays from all of us here at Zetetic! 🎄
2017-09-22 10:17:00 -0400
As noted earlier this year on our discussion forum, we’ll be discontinuing the iPad-only version of Codebook that’s currently available in the iTunes App Store. We’d like all our customers who purchased that version of the app to install the other, universal (i.e. runs on iPhone and iPad) version of Codebook now that it runs on both device types.
Previously, both apps used the same blue icon and had the same name on the Home screen, “Codebook”, making it hard to tell the apps apart. To aid in the transition and help give our iPad customers a heads-up that things are a-changing, we gave Codebook for iPad’s app icon an update, switching it to black and white.

Transitioning to the Universal Codebook
First, you’ll want to install the newest version of the universal Codebook for iOS app on your iPad alongside the old version with the black and white icon (don’t delete anything just yet!) Visit this link directly on your iPad to be taken to the right page in the App Store. If you don’t already own the iPhone version, not to worry: we created a bundle in the App Store allowing you to credit your iPad purchase towards the iPhone version, which should result in no charge for most customers.
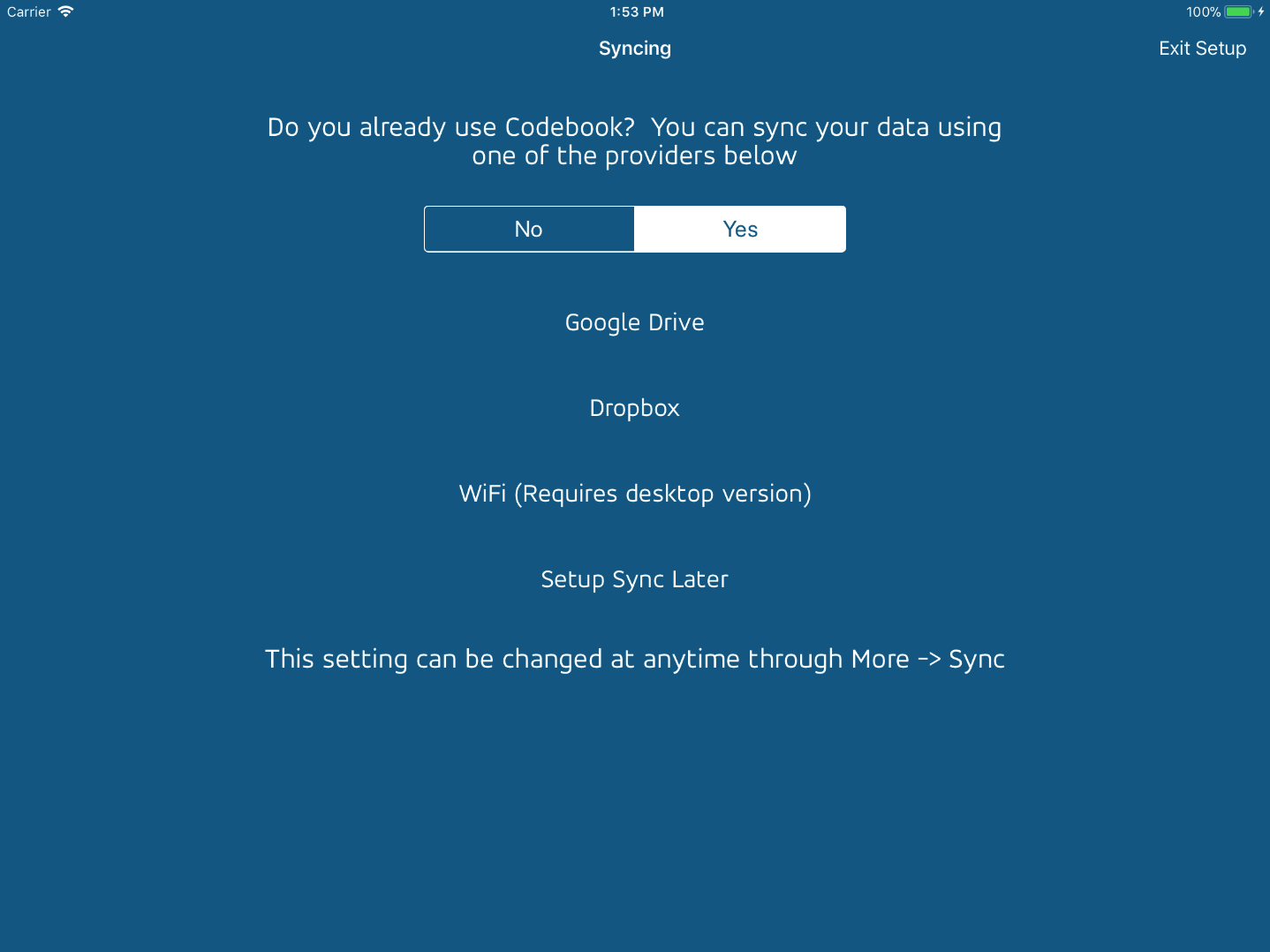
Once installed, launch the app and go through the first-time setup process, using the same password you usually use to protect your Codebook data.
During setup you will be given an opportunity to use Codebook’s Sync feature to copy your data over from another install of Codebook on the desktop via WiFi, or via Google Drive or Dropbox. You’ll want to set the switch on this screen to Yes for a restore.
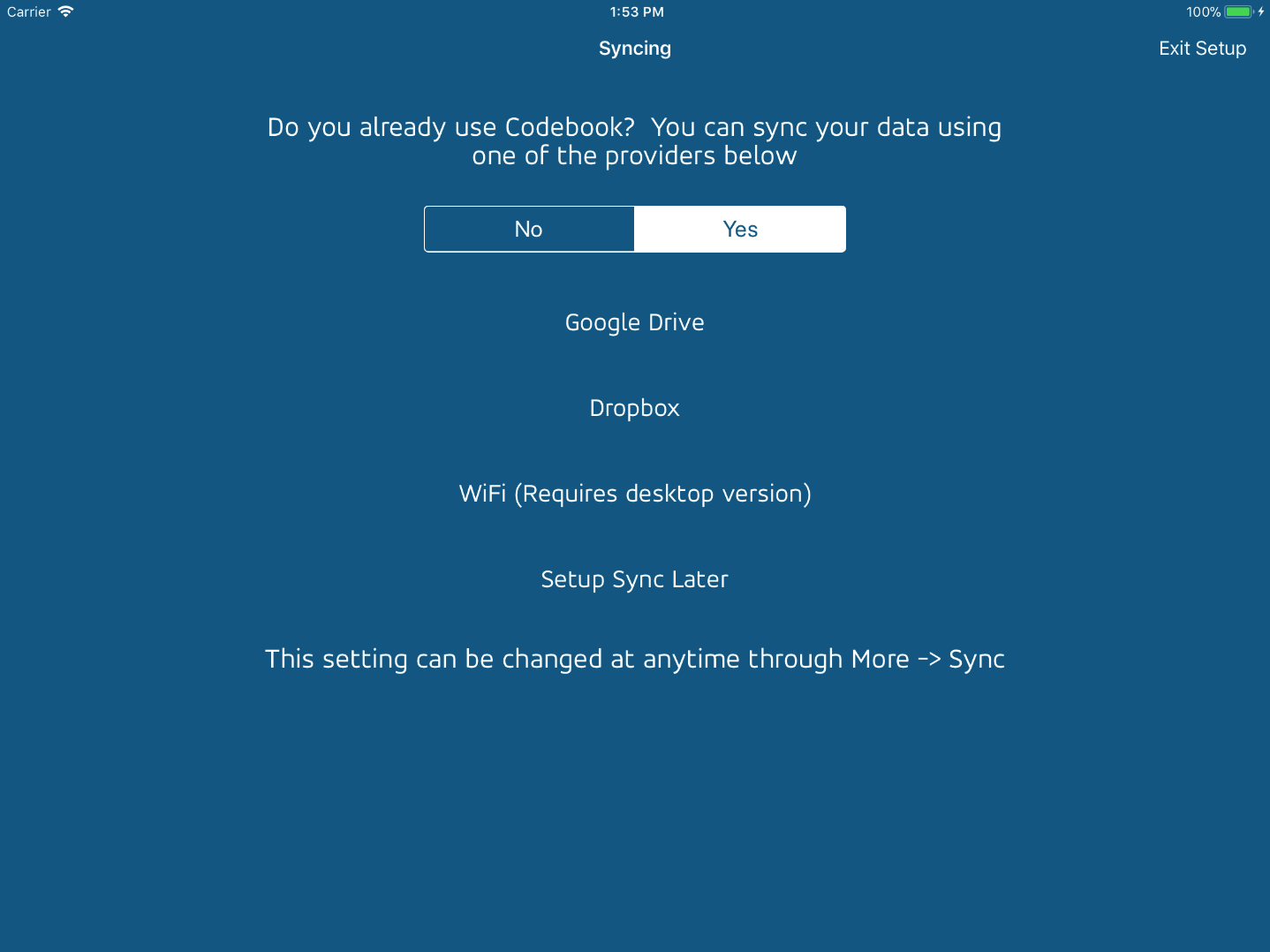
Once you’ve loaded your data into the universal build of Codebook (the one with the blue icon) you can safely remove the version with the black and white icon. Currently Codebook for iPad is still being maintained, but everyone using it should switch over to the universal version as soon as they can, as we will eventually remove it from the App Store.
2017-09-22 10:17:00 -0400
Properly configured projects using SQLCipher shouldn’t experience problems using Xcode 9. However, changes in the new SDKs can cause compile time errors for misconfigured projects, e.g.
Implicit declaration of function ‘sqlite3_key’ is invalid in C99
Implicit declaration of function ‘sqlite3_rekey’ is invalid in C99
We have prepared important recommendations for SQLCipher developers on how to resolve these problems on the SQLCipher support forums:
Important Advisory: SQLCipher with Xcode 9 and new SDKs
![]()